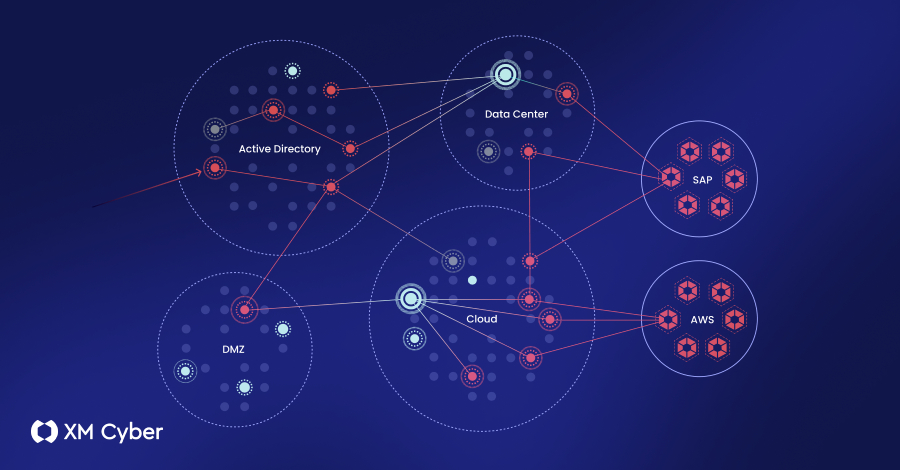
Cybersecurity's Two-Decade Blunders: Lessons Learned?
Twenty years of digital missteps have littered the cybersecurity landscape with cautionary tales. From major outages to the enduring relevance of outdated tech, the industry's track record is, frankly, a mess.