And here I thought we were supposed to be getting smarter. Apparently, doubling security budgets over half a decade and still seeing response times crawl means we’re just… spending more to stay in the same place. The folks over at Prophet Security, bless their data-driven hearts, are calling it out: hiring more analysts isn’t the silver bullet everyone’s been praying for. It’s the architecture, stupid.
The problem, as they lay it out, is that the whole Security Operations Center (SOC) model is still playing catch-up with a threat landscape that’s moved at warp speed. We built our systems assuming humans could manually sift through alerts at a pace that just doesn’t exist anymore. The business is spitting out alerts like a firehose, and we’re still trying to catch them with a teacup. It’s like bringing a butter knife to a chainsaw fight.
The Uncomfortable Math of the Modern SOC
Look, I’ve been around this block a few times. Twenty years of watching Silicon Valley hype cycle through, from the dot-com bust to the blockchain mania, and now AI everything. Every vendor promises the moon, every engineer is building something that could be useful, but the actual grunt work, the day-to-day grind of protecting systems, often gets lost in the shuffle. And these numbers from Mandiant and Crowdstrike? They’re not pretty. Median dwell time of 14 days. Threat actors handing off systems in 22 seconds. Yet, IBM’s Cost of a Data Breach research shows we’re still taking an average of 241 days to even identify and contain a breach. The math just doesn’t add up, and it’s not because our analysts aren’t working hard. They are. They’re drowning.
The industry doesn’t want to admit this. Why would they? It’s easier to sell you more tools, more training, more bodies. But Prophet Security points out the obvious: SOC teams have already done the low-hanging fruit. They’ve tiered severity, auto-closed the noise, suppressed the chatter, and tuned their rules till they’re blue in the face. None of that changes the fundamental problem: the sheer volume of actual alerts hitting human eyes still exceeds what any human team can investigate thoroughly.
Most breaches don’t trigger a high severity alert. Instead the first signs appear in a low severity alert that gets buried in a queue no human can clear.
This is the kicker, isn’t it? The silent killer. The low-severity alert, the one that doesn’t scream ‘Red Alert!’ but instead whispers ‘Hey, maybe check this out,’ gets lost in the daily deluge. We’re missing the early warning signs because our systems aren’t built to handle the scale. We can’t hire our way out of this hole. You can’t just throw more analysts at a broken process and expect miracles. You hire your way to marginal improvements, sure, but you can’t hire your way to fixing the fundamental model.
Is Your SOC Actually Working, Or Just Busy?
Before you go ordering more pizza for late-night shifts or start interviewing the tenth analyst this quarter, run this diagnostic from Prophet Security. It’s a quick gut check, no vendor jargon, just hard questions.
1. What percentage of alerts above your defined investigation threshold did your team actually investigate last quarter? If that number’s creeping below 90%, you’ve got a hole in your net. And it’s not because your people are slacking. It’s the workflow. More headcount won’t patch that hole.
2. How many detection rules has your team suppressed in the last 12 months without an engineering ticket to replace the coverage? Suppressing noise is good. Suppressing it and forgetting about it? That’s building a blind spot. You’ve just removed a guardrail, and the bad guys know it.
3. What was your senior analyst turnover last year, and how long did each replacement take to reach productive contribution? If your top talent is walking out the door at a clip, and it takes half a year to train someone new, you’re living on borrowed time. Your tribal knowledge is walking out with them.
4. If alert volume doubled tomorrow, what’s the first thing your team would stop doing? The honest answer here reveals where your program’s priorities are really at, and how fragile the whole operation is.
The AI Question: Savior or Just Another Buzzword?
Now, about this AI business. Prophet Security’s piece hints at it: AI can investigate every alert. That’s the theory, anyway. But who’s actually making money here? Is it the company selling the AI platform, or the struggling SOC team trying to make sense of its outputs? The danger, as always, is that we’ll just layer more complexity onto an already complex system, hoping AI magically fixes problems that are deeply rooted in our operational design. It’s not about replacing analysts, necessarily, but about augmenting them, freeing them up from the sheer volume game to focus on the truly complex threats. But will it? Or will it just be another expensive layer of abstraction that the CFO still can’t get a clear ROI on?
The article is clear: the gap isn’t closing with more bodies. It’s a systemic issue. And if AI is the answer, it needs to be an answer that addresses the architecture, not just the symptom of alert overload. The real question isn’t ‘Can AI do it?’ but ‘Can AI do it better, faster, and cheaper than our current, broken, human-centric model?’ For now, it’s a good bet that the expensive subscriptions will keep flowing, but the actual reduction in breach time might be as elusive as ever.
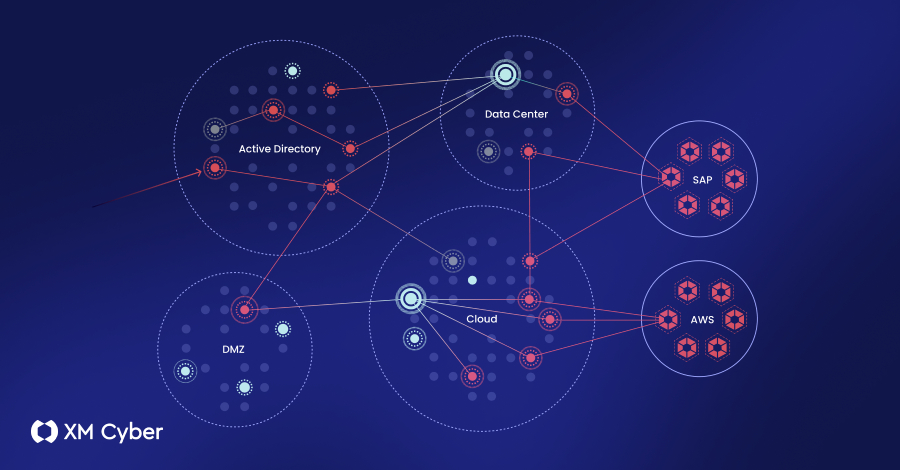
The Real Attack Surface: The Alert Queue
This is where the rubber meets the road. The alert queue is the attack surface. It’s the waiting room where threats fester. Prophet Security’s ebook goes into detail about why this is the case and how AI can change the game by actually processing every single alert, not just the ones that make it to the top of the human pile. It’s a fascinating idea, but as always, the devil is in the implementation details and, more importantly, the vendor’s profit margins.
This isn’t about a failure of individual effort; it’s about a failure of design. And until we address that design, more analysts will just mean more people staring at a screen, overwhelmed, while the real threats slip through the cracks.