Are security operations teams finally growing up? The agenda for Rapid7’s 2026 Global Cybersecurity Summit, unveiled recently, suggests a palpable shift away from the frantic, reactive fire-fighting that has defined the industry for too long. Instead, it lays out a roadmap for how security operations are evolving, aiming for earlier intervention, sharper prioritization, and a clearer understanding of what actually matters when the digital dust settles.
Day 1: Understanding the Adversary and the Modern SOC
The two-day event kicks off by dissecting the ever-shifting threat landscape and, crucially, how defense strategies must adapt. The opening keynote, Defense Starts Earlier Than You Think, hosted by Brian Castagna and IDC’s Craig Robinson, immediately tackles complexity as the primary hurdle to effective security. It’s not just about having the latest tools; it’s about fundamentally rethinking when and how defenses are deployed. This sets a pragmatic tone, moving beyond theoretical threats to the messy reality of keeping operations afloat.
Raj Samani and Rachel Tobac, among others, will then dive into The Reality of Running a SOC in 2026. Their discussion is expected to pivot from the ‘how’ attacks begin—identity misuse, cloud misconfigurations—to the persistent gap between evolving threats and defender capabilities. This isn’t new, but the framing suggests a deeper dive into the systemic issues that leave security teams perpetually playing catch-up.
What’s particularly interesting is the inclusion of Customer Panel: How Clarity Beats Complexity. Hearing CISOs from Netscout, Target RWE, and Culligan discuss simplifying environments and focusing on outcomes over mere activity provides a much-needed dose of real-world application. This panel, in particular, could offer actionable insights for other organizations drowning in alert noise and chasing vanity metrics.
The agenda then drills down into the day-to-day, with Inside the Modern SOC: Who Carries You Through an Incident. This session promises a step-by-step walkthrough of a real investigation, a crucial element often missing from high-level discussions. Understanding triage, decision-making under pressure, and how those choices shape outcomes is gold for practitioners.
And yes, AI makes its inevitable appearance. The AI Dilemma: Automating Defense Without Surrendering Judgment tackles the thorny questions of trust and transparency. The industry has been awash with AI hype; this session aims to ground the conversation in practical application—how AI truly supports analyst decision-making, rather than just automating it into oblivion. It’s a fine line, and one that many are still struggling to define.
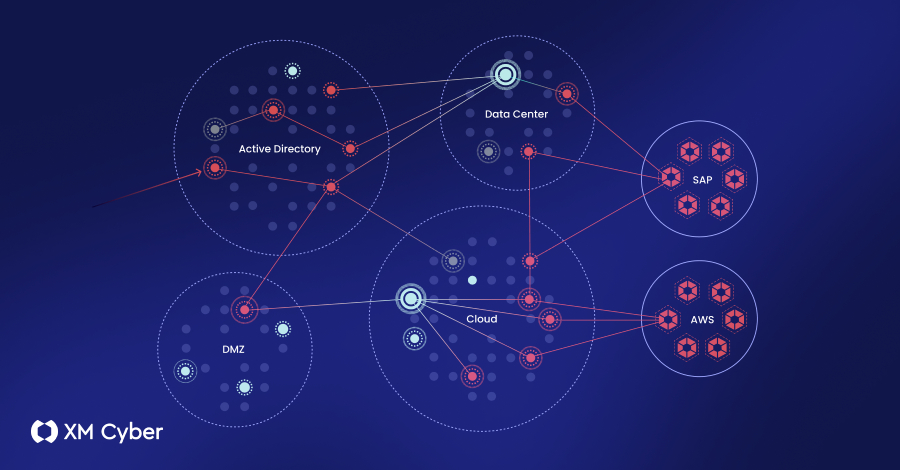
Beyond the Vulnerability List shifts focus to exposure management. This move from static vulnerability lists to using exposure as an early warning signal for detection and response is a logical progression. It’s about prioritizing what actually matters in the attack chain, not just ticking boxes on a compliance report. Coupled with Using Red Teaming to Power Preemptive MDR, which use adversary testing to validate detection and response, the day is building a case for proactive, intelligence-driven security.
The day’s closing, Persistence Under Pressure, featuring former Special Forces operator Jason Fox, offers a unique perspective. Drawing parallels between military operations and cybersecurity, it’s an attempt to extract lessons on preparation, adversary understanding, and decision-making in unpredictable environments. It’s a compelling angle, albeit one that could lean into the rah-rah if not carefully managed.
Day 2: Leadership and Practitioner Tracks - Bridging the Gap
Day two smartly bifurcates into tracks for leaders and practitioners, acknowledging that the challenges and solutions differ significantly. For CISOs, The CISO’s Role in Enterprise Transformation and How Exposure Insights Reframe Risk and Security Decisions promise to explore the evolving responsibilities of leadership beyond the technical. It’s about influence, risk articulation, and aligning security with broader business objectives—a necessary evolution for the role.
A CISO’s Guide to MDR Accountability and Outcomes tackles the perennial problem of measuring effectiveness. Shifting from activity metrics to genuine business impact is the holy grail of security leadership. This session could be a game-changer if it offers concrete frameworks.
Then, the Customer Panel: What CISOs Would Do Differently If Starting Today is likely to be a candid session. Learning from the hard-won experience of CISOs from Genesys and TSB Bank—what they’d simplify, what they’d avoid—offers invaluable retrospective wisdom.
For the practitioners on the ground, Hunt or Be Hunted: Frontline Tales of Detection promises raw incident analysis, focusing on analyst decision-making and signal correlation. The New Rules of Detection Engineering, with insights from Steve Edwards, dives into detection-as-code and signal prioritization, areas critical for building efficient detection capabilities.
From Cloud Exposure to Runtime Attack will dissect cloud attack scenarios, demonstrating how risks escalate and how to interrupt them. Finally, IR in Practice: Tools, Tradecraft, and Adversary-Informed Investigation aims to explain incident response by showcasing open-source tools and real-world workflows. It’s about making the complex digestible and the critical actionable.
Taken as a whole, the agenda for the 2026 Rapid7 Global Cybersecurity Summit isn’t just a schedule of talks; it’s a manifesto for a more mature, intelligent approach to security operations. The focus on earlier decisions, better prioritization, and outcome-driven strategies suggests that the industry might finally be leaving behind some of its most self-defeating habits. This is less about chasing the next scary headline and more about building a resilient, informed defense. It’s a welcome evolution, and one that deserves serious attention from anyone involved in protecting digital assets.
Taken together, the agenda reflects a shift that runs through every session. Security operations are moving toward earlier decisions, better prioritization, and a clearer understanding of what matters in the moment.
Will AI Really Change SOCs?
The repeated mention of AI, particularly in The AI Dilemma, indicates it’s no longer just a buzzword but a component being integrated into practical SOC workflows. The emphasis on judgment and transparency suggests a mature understanding of AI’s limitations and a focus on augmenting human analysts rather than replacing them wholesale. The real test will be in the specifics of how these tools are presented and the practical guidance offered to ensure AI enhances, rather than hinders, effective security operations.
Is Focusing on Exposure Management a Real Shift?
Indeed. The move from simply tracking vulnerabilities to managing exposure signifies a critical pivot. It acknowledges that not all vulnerabilities are equal, and that understanding how an asset is exposed to attack vectors is paramount. This implies a more dynamic and context-aware approach to risk, aligning security efforts with the actual likelihood and impact of a breach. This is a data-driven strategy that, if executed well, should lead to more efficient resource allocation and better threat mitigation.
🧬 Related Insights
- Read more: Apple Intelligence’s Shield Cracked: Hackers Sneak Past Your iPhone’s AI Brain Guards
- Read more: 80,000 Hikvision Cameras Exposed: Cybercriminals Auction Off Access
Frequently Asked Questions
What is the main focus of the 2026 Global Cybersecurity Summit?
The summit focuses on the evolution of security operations, emphasizing earlier detection, smarter decision-making, and outcome-driven strategies in the face of evolving threats.
How does the agenda address the role of AI in cybersecurity?
The agenda includes sessions specifically on AI’s role in the SOC, focusing on trust, transparency, and how AI can support analyst decision-making without compromising judgment.
What are the key themes for security leaders at the summit?
Themes for leaders include the evolving CISO role in enterprise transformation, how exposure insights reframe risk, and measuring MDR accountability through business outcomes.