So, your security team spent the quarter patching hundreds of vulnerabilities. The dashboards glow a reassuring green. Everyone high-fives. Then comes the inevitable, soul-crushing question from the C-suite: “Are we actually safer?” The room fills with that awkward silence we all know and loathe, because the honest answer—and most leaders suspect it—is probably not.
This isn’t a new problem, folks. It’s the perennial question that plagues every security team, regardless of size or budget. We’re drowning in data about what could go wrong, but starving for context about what actually poses a risk to our unique business operations. That’s where this whole “exposure management” racket comes in. The idea is noble: bridge the gaping chasm between closing tickets and actually reducing risk. The market, predictably, has responded with a tsunami of platforms, each promising the moon. But as always, the real question isn’t what they claim to do, but what they actually deliver. And more importantly, who’s cashing the checks for all this noise?
The Illusion of Security: Why Patch Counts Lie
For twenty years, I’ve watched Silicon Valley churn out solutions to problems that often don’t exist, or that they’ve only partially understood. This exposure management push feels eerily familiar. We’re told that if we just buy this new widget, our risks will magically shrink. But what are these platforms, at their core? The original article breaks them down into four flavors, and frankly, most of them are just different ways of packaging the same old limitations.
There are the stitched portfolio platforms. Think of them as a Frankenstein’s monster of cybersecurity. A big vendor gobbles up a bunch of smaller, specialized tools—a vulnerability scanner here, a cloud security gizmo there—and slaps their logo on it. They might make it look integrated, a unified console and all that jazz, but under the hood, each piece still operates in its own silo. They speak different languages, use different data models, and barely acknowledge each other’s existence. So, sure, you get a lot of findings, but correlating them? Understanding the chain of vulnerabilities that an attacker could exploit? Good luck.
Then you have the data aggregation platforms. These are the digital librarians of the security world. They ingest all the data your existing tools spit out, try to sort it into some kind of order, and present it nicely. The catch? They can only work with what they’re given. If your existing scanners are generating disconnected, context-free noise, well, you’ll just get a prettier version of that same disconnected noise. No magic correlation, no deeper insight. It’s like having a ton of raw ingredients but no chef.
Next up are the single-domain specialist platforms. These guys are really good at one thing. They might be masters of cloud misconfigurations, or they might have a laser focus on external attack surfaces. They can dig deep, and you’ll probably get some solid intel in their narrow niche. The problem? Real attackers don’t stick to one domain. They hop from a misconfigured S3 bucket to a stolen credential found on an internal server, or a forgotten CVE on an old piece of hardware. If your platform only sees one piece of the puzzle, you’re missing the bigger, scarier picture.
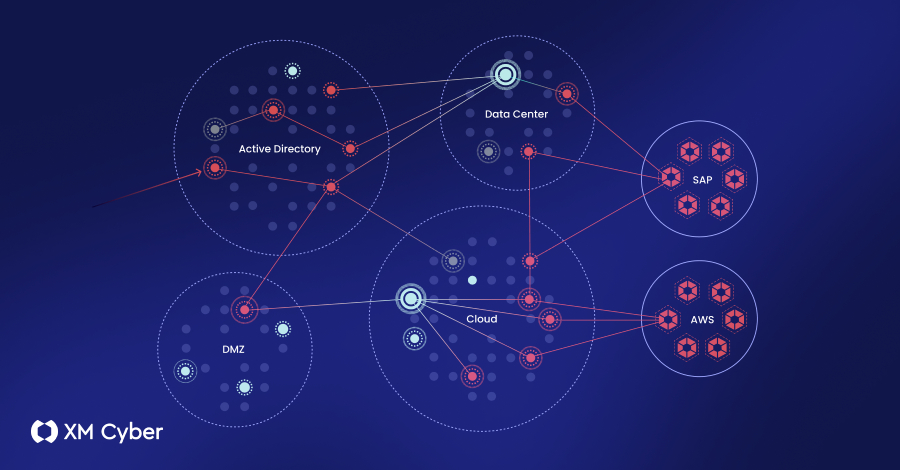
And finally, the so-called integrated platforms. These are the ones built from the ground up to actually understand how things connect. They’re designed to discover and correlate different types of exposures—think credentials, misconfigurations, exploitable vulnerabilities, identity issues—all within a single engine. The dream here is to build a digital twin of your environment, mapping out how an attacker could actually move from Point A to Point B, across your on-prem servers, your cloud instances, and everything in between.
The 5 Questions That Separate Hype from Help
Look, the architecture matters. It dictates what you can actually see, what you can trust, and what you can do about the threats you face. So, when you’re out there evaluating these shiny new platforms, don’t just nod along to the sales pitch. Start asking the tough questions.
1. What Can It Actually See, and How Deeply Does It Understand It?
This is foundational. Attackers don’t just exploit CVEs – those are only about a quarter of the picture. The rest? Think stolen credentials, sloppy configurations, permissions set to ‘give-everyone-the-keys,’ and a general mess of identity problems. Stitched platforms are limited by the lowest common denominator of their acquired parts. Aggregators are prisoners of the data feeds they inhale. Single-domain specialists are, well, specialists. A truly integrated platform should discover a broad range of exposure types natively – and keep up with the new stuff, like AI workloads and those pesky machine identities nobody talks about.
But just seeing something isn’t enough. What does the platform know about it? A platform that just slurps data from other tools is stuck with whatever superficial details those tools bothered to collect. The native discoverers have the advantage: they control the depth of intel on each exposure, from how easily it can be exploited to exactly how to fix it. If your platform misses certain types of exposures, that’s a blind spot. If it sees them but only gives you surface-level info, you’re just wading through noise.
2. Can It Map Attack Paths Across My Entire Environment?
Some stitched platforms will show you “attack paths,” but these are often just theoretical lines drawn between network points. They don’t model actual attacker behavior. Aggregators? They don’t show paths at all; you just get a list of unconnected issues. The real test is whether a platform can trace a path that crosses the boundaries of your different environments. An attacker grabbing cloud credentials from a compromised on-prem machine can bypass all your fancy cloud defenses because the exploit started outside the cloud’s watchful eye. A vulnerability that seems low-priority on its own might become a critical stepping stone if it allows access to a system with exposed credentials.
“The real test is whether the platform can trace paths across environment boundaries. An attacker who captures cloud credentials on-prem can bypass every cloud-native defense - because the path started outside the cloud platform’s visibility.”
This is where the truly integrated platforms shine. They’re building a connected map of your risk, not just a bulletin board of individual threats. They should be able to show you precisely how a weakness in your external web app could lead to a compromise of your sensitive customer data stored in the cloud, or how an unpatched server in your data center becomes the gateway to your remote workforce’s access tokens.
3. Does It Prioritize Risks Based on My Business Impact?
This is the million-dollar question, and the one most platforms fumble. They’ll tell you a vulnerability is “critical” based on CVSS scores or exploit availability. Great. But what if that vulnerability is on a server that hosts your marketing blog? Does it really matter as much as the same CVSS score on a server processing payroll? No. A platform’s true value comes from understanding your critical assets, your business processes, and mapping threats directly to the things that keep you in business. This requires deep asset inventory and contextualization. Many platforms just give you a generic risk score. You need one that’s tailored to your organization’s unique risk appetite and business priorities.
4. How Does It Handle Remediation – Beyond Just Telling Me What’s Wrong?
Finding is one thing. Fixing is another. A good exposure management platform shouldn’t just dump a list of problems on your desk. It should guide your teams toward effective remediation. Does it offer actionable remediation steps? Can it integrate with your ticketing system to automatically create tasks? Does it provide context to the folks doing the fixing so they understand the why behind the patch? Simply highlighting a vulnerability without providing a clear, efficient path to resolution is just creating more work. The best platforms will help orchestrate the fix, not just flag the failure.
5. Does It Actually Improve My Team’s Efficiency and Effectiveness?
This is the ultimate litmus test. After all the sales pitches and the dazzling demos, does this platform actually make your security team’s lives easier and their work more impactful? Or is it just another tool to manage, another dashboard to babysit, another source of alert fatigue? A platform that truly streamlines workflows, reduces manual effort in threat analysis, and provides clear, contextualized insights should demonstrably improve your team’s speed and accuracy in reducing risk. If it adds complexity or requires massive manual effort to extract value, it’s failing its core purpose.
Who’s Actually Making Money Here?
Let’s be blunt. The security market is booming, and every vendor wants a piece of the exposure management pie. Companies that have been selling individual point solutions are now stitching them together, hoping you won’t notice the seams. Others are aggregating data, providing a pretty dashboard over your existing chaos. And some, the integrated ones, are genuinely trying to solve a complex problem.
The folks making the most money right now are the vendors selling these platforms, especially the stitched and aggregated ones that can rebrand existing tech. They’re creating new categories and selling the dream of simplified security. For the end-user, the real win comes from identifying a platform that cuts through the noise and provides actionable intelligence tied directly to business risk, not just a vanity metric.
Ultimately, the goal isn’t a greener dashboard. It’s a more resilient business. And that requires more than just closing tickets. It requires understanding how the pieces fit together and how attackers can exploit them. Don’t get caught buying the illusion of security. Ask the hard questions. Your business depends on it.
🧬 Related Insights
- Read more: TeamPCP’s Ruthless Hijack of Security Scanners: 500K Machines, 300GB Stolen
- Read more: Bitter’s Hack-for-Hire Blitz Hits MENA Journalists, Echoing Indian Spy Reach
Frequently Asked Questions
What is exposure management? Exposure management is a security discipline focused on identifying, prioritizing, and remediating cyber threats that could lead to a data breach or operational disruption. It aims to provide context beyond simple vulnerability counts, linking technical weaknesses to actual business risk.
Are vulnerability scanners the same as exposure management platforms? No, vulnerability scanners are typically point solutions that identify known security weaknesses (like CVEs) on systems. Exposure management platforms aim to go further by correlating these vulnerabilities with other types of exposures (like misconfigurations and identity issues), mapping attack paths, and prioritizing remediation based on business impact.
How does an integrated platform differ from a stitched platform? An integrated platform is built from the ground up as a single system designed to discover and correlate various types of exposures. A stitched platform is a collection of separate tools acquired by a vendor and bundled together, often lacking deep correlation and unified data models between the original components.