What was everyone expecting from the threat landscape this spring? Probably more of the same – fileless malware, phishing emails with dodgy attachments, maybe the occasional zero-day exploit splashed across the tech pages. Standard fare. But this whole VENOMOUS#HELPER operation? It’s got a different flavor. This isn’t about dropping a malicious executable that antivirus scanners will flag in nanoseconds. This is about turning the tools businesses rely on for legitimate remote support into their own worst nightmare.
We’re talking about over 80 organizations, mostly in the U.S., according to Securonix, getting hit. And the modus operandi is unsettlingly clever: they’re using actual, signed Remote Monitoring and Management (RMM) software – specifically SimpleHelp and ScreenConnect – to gain a foothold. This isn’t some fly-by-night script kiddie operation; this looks like the work of an Initial Access Broker (IAB) or, more chillingly, a ransomware group laying the groundwork.
The Dual-Channel Dodge
Here’s the real kicker. The attackers aren’t just slopping one RMM tool onto a compromised machine. Oh no. They’re deploying both SimpleHelp and ScreenConnect. The researchers who dug into this (Akshay Gaikwad, Shikha Sangwan, and Aaron Beardslee) point out that this creates a “redundant dual-channel access architecture.” Translation: if one backdoor gets discovered and slammed shut, they’ve got a perfectly good backup ready to go. It’s like having a spare tire, but instead of a flat, it’s for when the entire road collapses.
And how do they get these legitimate tools onto machines that are supposed to be secure? It starts with a phishing email. This one impersonates the U.S. Social Security Administration (SSA) – a classic, because who doesn’t want to verify their SSA status? The email prompts the recipient to click a link to download a supposed SSA statement. This link, cunningly, doesn’t point to some shadowy corner of the dark web. It leads to a legitimate, but compromised, Mexican business website (gruta.com[.]mx). Smart. Email filters are much less likely to flag traffic originating from a known, albeit defaced, domain.
Once clicked, the user is directed to download an executable from a second attacker-controlled domain (server.cubatiendaalimentos.com[.]mx). This isn’t your garden-variety malware installer. It’s an executable responsible for dropping the SimpleHelp RMM tool. The attackers reportedly gained access to a single cPanel account on a legitimate hosting server to stage this binary. It’s a proof to how a single weak link can compromise an entire chain.
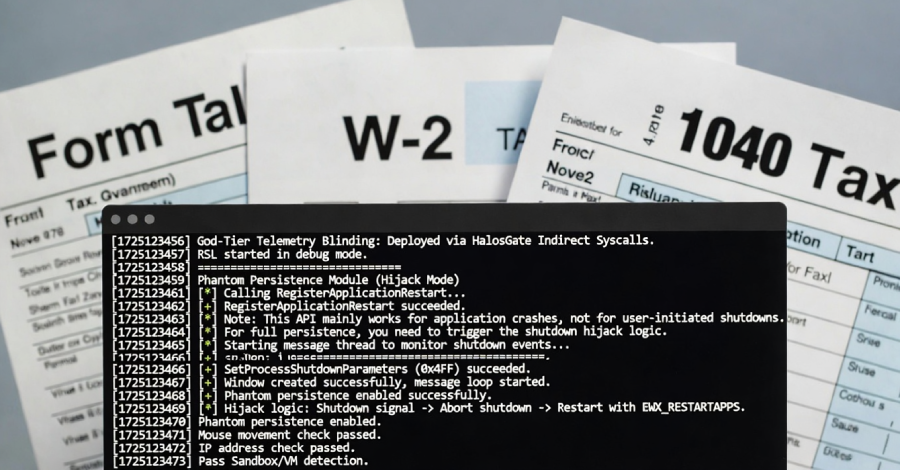
Persistence is Key (and Terrifying)
Once the victim opens the executable (thinking, bless their heart, it’s a document), the real work begins. The malware installs itself as a Windows service, using Safe Mode persistence. That means it’s tough to dislodge. But they didn’t stop there. It boasts a “self-healing watchdog” – a nasty little feature designed to restart the RMM service if it gets terminated. It’s like a persistent cough you just can’t shake. And every 67 seconds, it’s checking registered security products and polling user presence every 23 seconds, essentially watching the digital room.
To enable that fully interactive desktop access, the SimpleHelp client snags SeDebugPrivilege – a fancy way of saying it gets elevated permissions. And it uses elev_win.exe, a legitimate file associated with SimpleHelp, to gain SYSTEM-level privileges. This allows the attacker to see your screen, type your passwords, and generally snoop around your computer as if they were sitting right there. All while antivirus software sees nothing but a “legitimately signed software from a reputable U.K. vendor,