Tax season’s coming, and so are the digital wolves.
Forget noisy, blustering attacks. The latest maneuver from China-based cybercrime group Silver Fox is a masterclass in stealth and manipulation, slithering its way into organizations in Russia and India through a newly minted malware dubbed ABCDoor. It’s not just another piece of code; it’s a proof to how threat actors are constantly refining their art, using the very tools that govern our economies—taxes—as their Trojan horse.
And here’s the thing: this isn’t some fly-by-night operation. These attacks are meticulously crafted, mimicking official notices from the Income Tax Department. Imagine opening an email, thinking it’s about a routine audit or a list of violations, only to find a digital serpent waiting within. Kaspersky’s analysis paints a chillingly precise picture: these phishing emails lead users to download archives containing a modified, Rust-based loader. This loader, a repurposed piece of open-source code, then acts as the initial key, unlocking the door for the more potent ValleyRAT backdoor, and eventually, ABCDoor itself.
The Anatomy of Deception: Beyond Simple Phishing
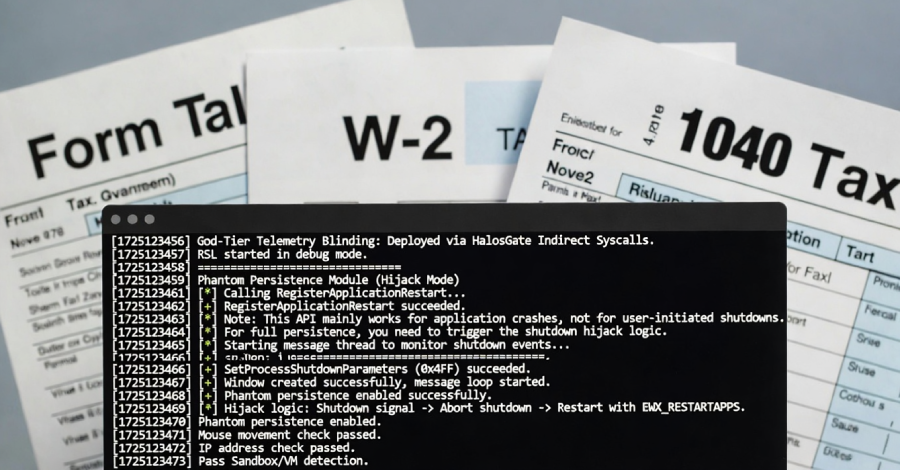
This campaign didn’t just materialize; it’s been brewing. The underlying architecture, a modified RustSL shellcode loader, has been in Silver Fox’s toolkit since late last year. What makes this particular iteration so unnerving is its sophistication in evading detection. It’s not just about hiding; it’s about actively checking its environment. The custom RustSL variant implements geofencing and environment checks, specifically looking to see if it’s running in a virtual machine or a sandbox—the very tools security researchers use to analyze malware. It’s like a burglar checking for alarm systems before attempting to break in.
Furthermore, the malware exhibits a particularly nasty persistence mechanism, playfully nicknamed Phantom Persistence. This isn’t your run-of-the-mill registry hack. Instead, it cleverly intercepts the system shutdown signal, fakes an update to trick the OS into rebooting, and then ensures its own execution upon startup. It’s a digital ghost that refuses to be exorcised, haunting the compromised system with sheer tenacity.
ABCDoor: The Evolving Backdoor
The ultimate payload, ABCDoor, is where the real damage can be done. This Python-based backdoor, previously undocumented, is the culmination of the attack chain. It establishes secure HTTPS communication with external servers, allowing for command execution, data exfiltration—including sensitive clipboard contents—remote control of the mouse and keyboard, and system process management. It’s a Swiss Army knife for digital espionage and financial crime, capable of adapting its functions on the fly through module updates. The evolution is rapid; in November 2025, Silver Fox was seen using JavaScript loaders, but newer RustSL versions have already expanded their geographical scope to include Japan, underscoring the group’s agile and expanding operational footprint.
The sheer scale is also noteworthy, with over 1,600 phishing emails flagged in just the first month of the year. India, Russia, and Indonesia are bearing the brunt, with South Africa and Japan also in the crosshairs. This isn’t a broad sweep; it’s precision targeting, adapting to local issues and work characteristics. As one analyst from S2W noted:
The Silver Fox group primarily utilizes highly customized spear phishing techniques for initial infiltration, deploying sophisticated and diversified attack scenarios tailored to the seasonal issues of the target country and the target’s work characteristics.
This points to a threat actor that is deeply invested in understanding its targets, moving beyond generic attacks to highly contextualized campaigns. It’s like a seasoned con artist who knows your neighborhood, your routine, and your vulnerabilities inside and out.
A Shift in the Landscape: More Than Just Malware
What’s truly fascinating—and frankly, a little alarming—is the platform shift happening before our eyes. We’re not just seeing new malware; we’re witnessing the evolution of attack vectors into something far more integrated with legitimate software development practices. The use of modified open-source components, like RustSL, and the sophisticated evasion techniques point to a threat landscape where attackers are increasingly acting like developers, albeit for nefarious purposes. They’re scavenging, adapting, and building modular tools that can be deployed rapidly and effectively across diverse targets.
This isn’t just about preventing phishing emails; it’s about understanding the underlying currents of how digital infrastructure is being weaponized. The ability of Silver Fox to pivot from opportunistic financial gains to espionage, and to constantly adapt its tools and targets, paints a picture of a threat that’s not static but dynamic, always learning and always evolving. It’s a reminder that in the grand theater of cybersecurity, the show—and the threats—never truly end.
What does this mean for businesses?
It means vigilance isn’t a buzzword; it’s a prerequisite for survival. It means looking beyond the obvious and understanding the subtle, sophisticated methods being employed. The digital world is our new frontier, and it’s being actively contested by actors who are as innovative as they are malicious. The question isn’t if we’ll be targeted, but when, and how well-prepared we’ll be to defend ourselves against these increasingly intelligent and adaptive adversaries.
🧬 Related Insights
- Read more: 81% of Developers Are Vibe Coding—And It’s a Security Nightmare
- Read more: North Korean Hackers’ Slick Slack Trick: Inside the Axios npm Compromise
Frequently Asked Questions
What is ABCDoor malware? ABCDoor is a newly discovered Python-based backdoor malware deployed by the China-based cybercrime group Silver Fox, used to facilitate remote access, data exfiltration, and system control on compromised machines.
How does Silver Fox deliver ABCDoor? Silver Fox primarily uses sophisticated, tax-themed phishing emails. These emails lead to archives containing malicious loaders that, in turn, download and execute the ABCDoor backdoor.
Which countries are targeted by Silver Fox? Recent campaigns have specifically targeted organizations in India and Russia, with additional focus noted in Indonesia, South Africa, and Japan.