Telegram Scams Go App-like.
It’s a tale as old as time: convenience breeds carelessness. And now, it seems, Telegram’s slick Mini Apps are the latest playground for digital brigands. Researchers have pulled back the curtain on FEMITBOT, a sprawling fraud operation that’s weaponizing these handy in-app experiences for everything from crypto scams to pushing outright malware onto unsuspecting Android phones.
Here’s the thing about Telegram Mini Apps: they’re designed to be frictionless. Think quick payments, simple tools, all without ever leaving your chat. Handy, right? Too handy, apparently. Cyber sleuths at CTM360 have detailed how this FEMITBOT platform crafts convincing, app-like facades directly within the messaging giant. It’s the digital equivalent of a wolf in sheep’s clothing, only the sheep is now a slick UI that feels perfectly integrated.
The Phishing Playbook
What’s FEMITBOT actually doing? Plenty, and none of it good. The operation spins up fake cryptocurrency platforms, masquerades as legitimate financial services, and even conjures up convincing AI and streaming site fronts. Brands? They’re just costumes. Apple, Coca-Cola, Disney – you name it, they’ve probably worn its digital face. This isn’t just a single scam; it’s an adaptable infrastructure. Attackers swap branding, languages, and themes on a whim, all while using the same backend. It’s a hydra of fraud, constantly regenerating.
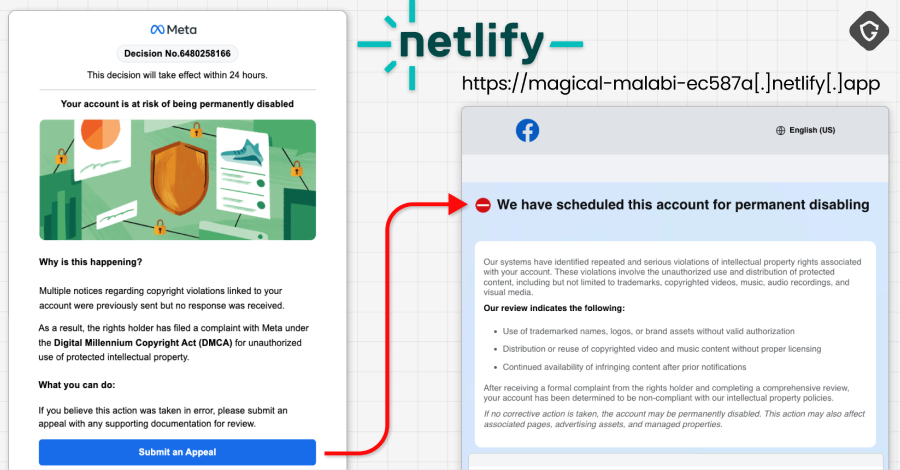
When you interact with one of these scam bots, that “Start” button doesn’t just open a chat. It launches a Mini App, presenting a phishing page within Telegram’s built-in browser. It looks like it belongs. Inside, victims are greeted with phantom balances, fabricated “earnings,” and the usual digital confetti designed to trick you into believing you’ve stumbled onto a goldmine. Urgency is the name of the game; countdown timers and fleeting offers are standard fare.
Want to cash out your fake winnings? Prepare to deposit real money or, predictably, complete referral tasks. It’s the advance-fee scam’s latest iteration, cloaked in a Mini App. And the tracking? Oh yes, they’re tracking. Meta and TikTok pixels are baked in, presumably to fine-tune their con artistry and measure just how many people they’ve fooled.
“The APK filenames are carefully chosen to resemble legitimate applications or use random-looking names that don’t immediately trigger suspicion.”
Malware in the Miniature
But wait, there’s more. Some of these Mini Apps aren’t just after your crypto. They’re actively pushing malware disguised as legitimate applications. Think BBC, NVIDIA, CineTV – all co-opted to deliver Android APKs. Users are nudged to download these files, click suspicious links, or install web apps that mimic the real deal. The APKs themselves are hosted on the same domains as the phishing sites, complete with valid TLS certificates to avoid those pesky browser warnings that might tip off the less-than-attentive.
It’s a clever, albeit malicious, integration. By hosting the malware alongside the phishing content, attackers sidestep browser security flags and make the whole operation appear more legitimate. This is precisely why casual users, those less steeped in the ways of digital security, are particularly vulnerable. They see a familiar brand, a slick interface within an app they already trust, and the warning bells simply don’t ring.
My Take: The Inevitable March of Convenience
This whole FEMITBOT saga isn’t just about Telegram. It’s a symptom of a larger, more concerning trend: the relentless pursuit of convenience at the expense of security. Every new feature designed to make our digital lives easier, more integrated, and less friction-filled, also creates a new attack vector. We crave smoothly experiences, and attackers are more than happy to exploit that desire. The metaverse will have its own scams. IoT devices will be compromised. And yes, messaging apps will continue to be battlegrounds. The innovation cycle in cybersecurity is a grim reflection of innovation elsewhere; for every step forward in user experience, there’s a shadowy figure trying to weaponize it.
Should You Ditch Telegram?
Probably not, unless you’re prone to falling for obvious crypto scams. The advice is simple, yet often ignored: be wary of Telegram bots pushing crypto investments or pushing Mini Apps, especially if they ask for deposits or downloads. And for the love of all that is digital, stop sideloading APKs like they’re going out of style. Stick to official app stores. It’s not foolproof, but it’s a damn sight better than clicking on a link from a bot you barely trust.
This incident underscores a persistent problem: the blurring lines between trusted platforms and malicious actors. As applications become more integrated, so do the threats they can harbor. Vigilance isn’t just a good idea; it’s a necessity.