Look, we all expected AI to change the world. We pictured sentient robots and self-driving cars zipping us through utopian cityscapes. But what if the real platform shift isn’t about super-intelligence, but about massively amplified human ingenuity – including the ingenuity of those who want to do us harm? That’s where this whole AccountDumpling operation comes into play.
For months, the whispers were about more sophisticated nation-state attacks, zero-days, and quantum-resistant encryption. We were prepping for the high-stakes chess match. Instead, we’re staring down a swarm of highly organized, commercially driven attackers wielding off-the-shelf tools like Google AppSheet and Telegram like a scalpel to carve out tens of thousands of Facebook accounts. It’s less a cyber-armageddon and more a meticulously orchestrated digital heist on an industrial scale.
This isn’t just another phishing campaign. This is a glimpse into a darkly commercialized underworld where stolen digital identities aren’t just collateral damage; they’re the product. Guardio’s discovery paints a picture of a “living operation” – not a static kit, but a dynamic, evolving beast. Think of it like a digital hydra, constantly regenerating and adapting.
The Invisible Hand of AppSheet
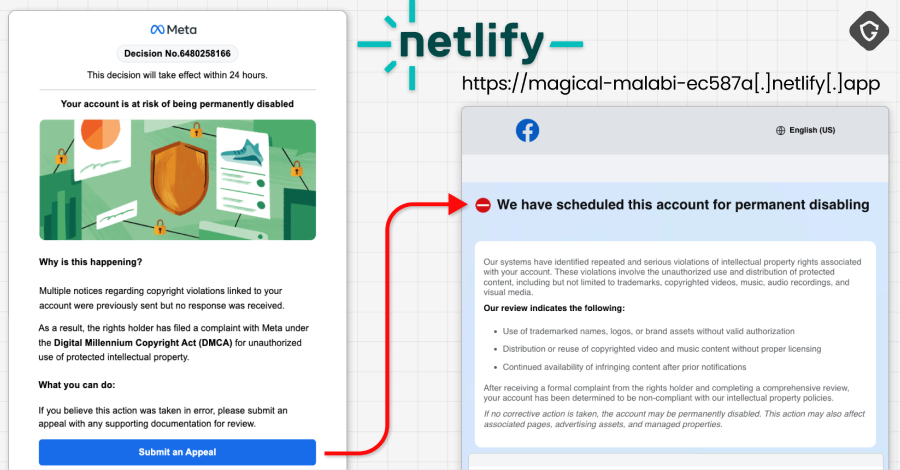
What’s truly wild is how they’re using Google AppSheet. Normally, this is a tool for businesses to build simple apps without deep coding knowledge – a democratizer of digital tools. Here? It’s been weaponized. The attackers are sending phishing emails from legitimate-looking AppSheet addresses, like [email protected]. Why? Because these fly right under the radar of most spam filters. It’s like using a doctor’s coat to sneak into a hospital – a deceptive but incredibly effective camouflage.
The emails themselves are a masterclass in psychological manipulation. They’re crafted to induce panic, mimicking official Meta communications. Account disablement, copyright complaints, verification reviews, even fake job offers from big-name companies like Apple and Coca-Cola – the lures are varied, designed to hit different anxieties. The goal? To scare you into clicking a link, straight into a trap.
“What we found wasn’t a single phishing kit. It was a living operation with real-time operator panels, advanced evasion, continuous evolution and a criminal-commercial loop that quietly feeds on the same accounts it helps steal back.”
A Criminal Ecosystem Unveiled
Once you’re hooked, you’re funneled into a labyrinth of fake login pages, CAPTCHA checks, and requests for sensitive data – your credentials, 2FA codes, even government ID photos. All of this information is then exfiltrated, often to Telegram channels. These channels, according to Guardio, are acting as the central nervous system, holding data from around 30,000 compromised accounts. That’s a staggering number, representing not just compromised logins, but entire digital personas ready to be sold.
This isn’t just about stealing passwords. It’s about stealing identity. These accounts have value – ad reputation, business legitimacy, even the ability to recover other accounts. It’s a full-spectrum assault on a user’s digital life.
Why This Matters: The Platform Shift in Action
This AccountDumpling operation is a profound indicator of the evolving threat landscape. It demonstrates how easily sophisticated criminal enterprises can co-opt legitimate platforms – Google, Telegram, Canva, Netlify, Vercel – to build their infrastructure. It’s a stark reminder that in the age of AI and interconnected services, the lines between legitimate tools and criminal enablers are blurring with alarming speed.
What strikes me most is the sheer human element behind this. Guardio’s report points to a Vietnamese name, PHẠM TÀI TÂN, associated with the PDFs used in the campaign. This isn’t some faceless botnet; it’s an organized group with a business model, selling stolen assets on the dark market. They are using the very platforms designed to empower individuals and businesses, twisting them into tools of mass exploitation. It’s a chilling proof to how easily powerful, user-friendly technologies can be repurposed for ill intent.
We need to move beyond thinking of cybersecurity as just technical defenses. This is about understanding the human psychology exploited, the social engineering at play, and the economic incentives driving these operations. The future of security isn’t just about firewalls; it’s about an informed, vigilant, and adaptable populace, armed with the knowledge of how these new digital tools can be turned against them.
The Silent Trade in Stolen Accounts
This operation highlights a critical, often overlooked aspect of the digital economy: the thriving black market for compromised accounts. Stolen Facebook accounts are not just discarded data; they are commodities. Their value lies in their established history, their advertising credibility, and their network connections. Threat actors can use these assets for a variety of nefarious purposes, from spreading misinformation and spam to executing further scams, effectively renting out the victim’s digital reputation.
The Ubiquitous Telegram Channel
It’s fascinating, and frankly unnerving, how consistently Telegram appears in these types of operations. Its relative anonymity, end-to-end encryption, and channel functionality make it an ideal — and apparently highly desirable — tool for threat actors to manage stolen data and communicate. The speed at which information can be shared and disseminated through Telegram channels makes them a powerful asset for these criminal networks.
🧬 Related Insights
- Read more: LockBit’s Ransomware Rampage Reignites the Fire
- Read more: Nation-State Cyber Threats: APT Groups, Tactics, and Defense Strategies
Frequently Asked Questions
What is Google AppSheet being used for in this attack? Google AppSheet is being used as a platform to host phishing content and send emails, allowing attackers to bypass spam filters and appear more legitimate.
How many accounts were affected? Approximately 30,000 Facebook accounts are estimated to have been compromised in this campaign.
Will I get my account back if it’s compromised? Account recovery can be difficult once credentials and 2FA codes are stolen. Victims should immediately attempt to secure their account through official Meta channels and report the compromise.