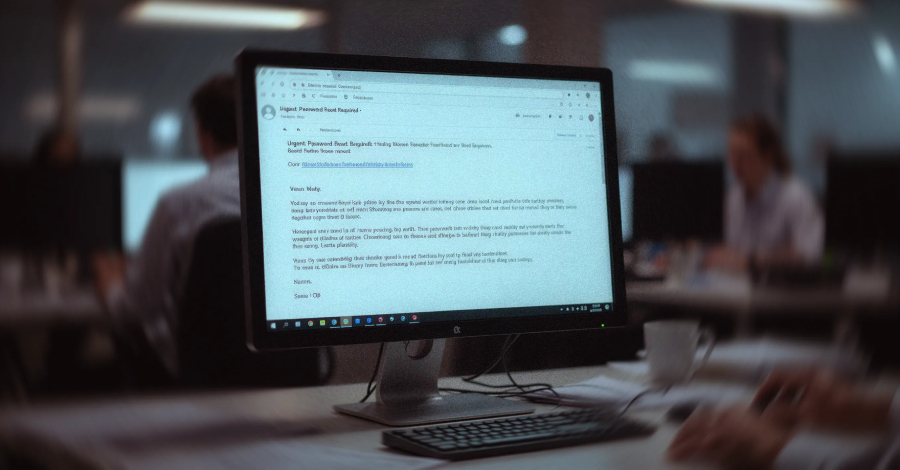
You’re staring at your inbox, trying to sort the signal from the noise. A notification about a pending invoice. A request to re-verify your account with a familiar service. Looks legit, right? Except it’s not. And the folks sending it don’t care about legitimate business; they’re just looking to skim your credentials, or worse. This isn’t new, but the scale? That’s what’s changing. Amazon’s Simple Email Service (SES) — a tool many of us rely on for legitimate communication — is increasingly becoming the go-to for phishers looking to bypass security filters. And frankly, it’s working way too well.
Look, I’ve been covering this stuff for two decades. I’ve seen fads come and go, seen companies paint over the same old problems with fresh coats of AI-powered pixie dust. But this? This is a classic case of a legitimate service becoming a convenient vector for bad actors, and the underlying issue is as old as time: exposed credentials.
The ‘Trusted’ Alias
Here’s the dirty little secret: Amazon SES is, by its very nature, a trusted entity. When an email comes from SES, it’s supposed to pass authentication checks like SPF, DKIM, and DMARC. Why? Because it’s Amazon. They have a reputation to uphold. Phishers know this. They’re not stupid. They’re just opportunistic. By piggybacking on SES, they sidestep a whole layer of security that’s designed to catch sketchy, unknown senders. It’s like using a celebrity’s endorsement to sell snake oil — the name carries weight, even if the product is garbage.
How Did We Get Here?
Kaspersky researchers are sounding the alarm, and their report points to a clear culprit: publicly exposed AWS Identity and Access Management (IAM) access keys. Think of these keys as the digital equivalent of a master key to a building. If someone leaves them lying around on GitHub, in a forgotten .env file, or even in a backup you thought was private, well, suddenly the bad guys have a free pass. Bots, like the ones built on TruffleHog, are constantly crawling these public spaces, sniffing out these keys. Once they find one with email sending permissions and decent limits, they’re off to the races.
“After verifying the key’s permissions and email sending limits, attackers are equipped to spread a massive volume of phishing messages,” Kaspersky explains.
It’s a streamlined process. Find keys, validate permissions, blast emails. Unprecedented abuse, they say. And it makes sense. Why bother setting up your own unreliable mail server when you can just borrow Amazon’s, and it’s practically free or dirt cheap if you’re just squatting on someone else’s compromised account?
The Scammers’ New Toolkit
What’s particularly galling is the quality of these phishing emails. It’s not just poorly formatted spam anymore. These actors are crafting custom HTML templates that mimic real services with uncanny accuracy. They’re building realistic login flows. We’re talking fake DocuSign notifications leading to AWS-hosted phishing pages, and sophisticated Business Email Compromise (BEC) attacks where fabricated email threads make fake invoices look disturbingly legitimate. Finance departments, you’re in their crosshairs.
Why Blocking IPs Isn’t Enough
So, what’s the solution? Well, the obvious one — blocking the IP addresses of the offending servers — is a non-starter. If you block the SES IP ranges, you’re not just blocking phishers; you’re blocking legitimate emails from Amazon customers. That’s not a viable option. It’s like trying to stop a single drop of poison by draining the entire well.
The Real Fix: Defense in Depth
Kaspersky’s recommendations are the standard, sensible advice you’d expect: the principle of least privilege for IAM permissions, multi-factor authentication everywhere, regular key rotation, and encryption. These are the basics. If your organization isn’t doing these things religiously, you’re already leaving the door wide open. The problem here is that a lack of these basics on a massive scale, specifically within the vast public cloud infrastructure, creates this breeding ground. It’s not just about securing your own house; it’s about recognizing that your neighbor leaving their doors unlocked makes your neighborhood less safe.
What this highlights, beyond the specific abuse of SES, is the ongoing struggle for attribution and containment in cloud environments. When a service is as ubiquitous and flexible as Amazon SES, it will inevitably be a target for abuse. The real vulnerability isn’t the service itself, but the human and procedural failures that allow its credentials to be compromised and misused at scale. We’re still playing catch-up, always have been, with the bad guys who are just looking for the path of least resistance. And right now, that path leads straight through a compromised AWS key and a seemingly innocent email from Amazon.
Who is Actually Making Money Here?
Let’s cut through the noise. Who benefits from this particular brand of chaos? Obviously, the threat actors. They’re making money by stealing credentials, tricking people into sending payments, or selling access to compromised accounts. But who else? Well, you could argue that the security companies selling the tools to detect these breaches, the consultants helping companies implement “least privilege,