Everyone thought the playbook was getting stale. Ghostwriter, that well-worn alias for a Belarus-aligned outfit known for its cyber-espionage and influence ops across Eastern Europe, was expected to keep tinkering with its usual kit – PicassoLoader, Cobalt Strike, maybe a WinRAR zero-day thrown in for good measure. But the latest campaign, observed since March 2026, signals a significant tactical shift. We’re not just talking about updated lure documents; this is about a smart, layered approach designed to filter out the noise and focus fire. This changes how we need to think about attribution and the sheer agility of these groups.
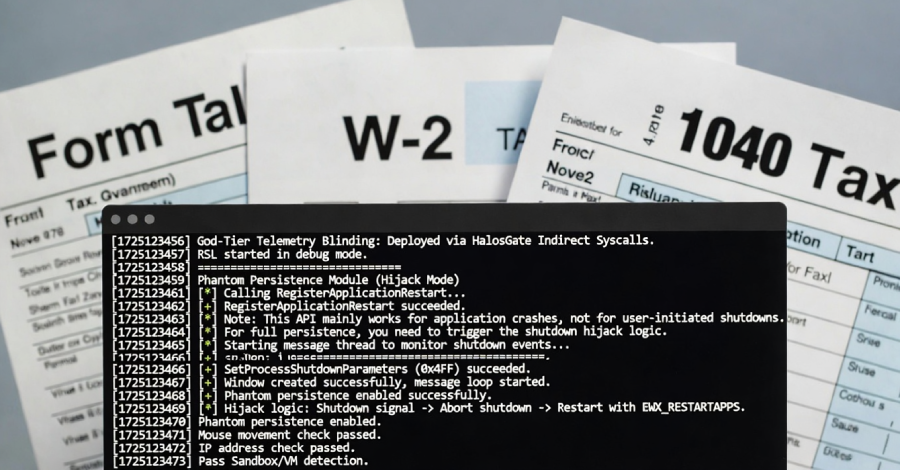
This isn’t your grandfather’s phishing. The current modus operandi involves malicious PDFs sent via spear-phishing attachments. The real twist? A geofencing check. Victims outside Ukraine receive a benign PDF. For those within the country’s digital borders, however, the embedded link in that seemingly innocuous document springs to life. It pulls down a RAR archive, which, in turn, unpacks a JavaScript payload. This payload does two things: it displays a decoy lure document – likely to keep the victim engaged and unaware – while simultaneously launching the PicassoLoader in the background. It’s a subtle, yet profoundly effective, way to isolate targets and minimize broad exposure.
The PicassoLoader itself isn’t just a simple downloader. It’s designed to profile and fingerprint the compromised host. Think of it as a digital reconnaissance mission. This collected data—the system’s specs, its network configuration, essentially its digital DNA—is then transmitted to attacker-controlled infrastructure every 10 minutes. This allows the Ghostwriter operators to manually assess whether the victim is valuable enough for the next stage: a potential third-stage JavaScript dropper for Cobalt Strike Beacon. It’s a deliberate, almost patient, approach that prioritizes quality over quantity, a far cry from the indiscriminate spray-and-pray campaigns of yesteryear.
A Data-Driven Approach to Targeting
This geofencing and host-profiling strategy isn’t merely a technical flourish; it’s a market analysis writ large in code. Ghostwriter is treating its targets like a market segment, meticulously vetting each potential customer before committing resources. The data collected allows them to move beyond crude IP-based targeting and understand the true value of a compromised system. This level of sophistication in operational planning is what sets persistent threat actors apart. They aren’t just attackers; they’re strategic actors with a clear understanding of resource allocation and risk mitigation.
This latest evolution in Ghostwriter’s arsenal, detailed by ESET and observed since March 2026, primarily targets military, defense, and governmental organizations within Ukraine. It’s a laser focus, contrasting with their broader victimology observed in countries like Poland and Lithuania, where industrial, healthcare, and logistics sectors have also been in their sights. This suggests a specific strategic objective tied to the ongoing geopolitical situation.
“FrostyNeighbor remains a persistent and adaptive threat actor, demonstrating a high level of operational maturity with the use of diverse lure documents, evolving lure and downloader variants, and new delivery mechanisms. This newest compromise chain that we detected is a continuation of the group’s willingness to update and renew its arsenal, trying to evade detection to compromise its targets.”
This quote from ESET researcher Damien Schaeffer perfectly encapsulates the dynamic nature of these threats. It’s a constant arms race, and Ghostwriter is clearly investing heavily in staying ahead of the curve. The phrase ‘operational maturity’ here isn’t just jargon; it signifies a group that understands the business of cyber warfare, optimizing its processes for maximum impact and minimal detection.
And it’s not just Ghostwriter. The disclosure comes as the Russia-affiliated Gamaredon group is also implicated in a spear-phishing campaign against Ukrainian state institutions, deploying GammaDrop and GammaLoad. HarfangLab notes Gamaredon’s strength isn’t in technical novelty, but in relentless tempo and scale. This simultaneous activity from different, yet ideologically aligned, groups underscores the sustained, multi-pronged pressure being applied.
Why Does Ukraine Remain a Primary Target?
The persistent targeting of Ukraine by various threat actors, including Ghostwriter and Gamaredon, isn’t accidental. It’s a direct reflection of the ongoing conflict and the strategic importance of information and disruption. For groups like Ghostwriter, whose activities are linked to Belarus and, by extension, Russia, these cyber operations serve as a digital front line, complementing kinetic actions. The objective is clear: to gather intelligence, disrupt government functions, and potentially sow discord. The data-driven tactics we’re seeing now only serve to amplify their effectiveness.
The PR Spin vs. The Reality
While the technical details are critical, it’s important to look past the purely technical descriptions. Reports often highlight the ‘evolution’ and ‘sophistication’ of these groups. This is true, but it’s also the language used to frame these actors as almost abstract entities. What we’re seeing is a calculated, almost coldly logical application of technology to achieve specific geopolitical and intelligence objectives. The ‘lure documents’ aren’t just clever tricks; they are carefully crafted pieces of social engineering designed to exploit human trust and operational processes. The ‘dynamic CAPTCHA checks’ and ‘server-side victim validation’ aren’t just evasion techniques; they’re sophisticated filters ensuring that the expensive malware payloads are only deployed against assets deemed truly valuable.
What Does This Mean for Defense?
For defenders, the implications are stark. The traditional perimeter-based security models are increasingly inadequate. The focus must shift to a more proactive, intelligence-driven defense. This means understanding not just what tools are being used, but why and how they are being deployed. Geofencing and host profiling aren’t theoretical concepts; they are active threat vectors. Organizations must invest in advanced endpoint detection and response (EDR) capabilities, strong threat intelligence feeds, and, crucially, continuous user training. The human element remains the weakest link, and these campaigns are expertly designed to exploit it.
The Ghostwriter campaign, with its geofenced PDFs and data-driven reconnaissance, represents a significant step up in operational effectiveness. It’s a clear signal that threat actors are becoming more efficient, more strategic, and more dangerous. The days of simply blocking known bad IPs are long gone. It’s time for defenders to adapt, or risk becoming the next victim in this evolving digital war.
🧬 Related Insights
- Read more: Cybersecurity Summit Agenda: Security Ops Getting Smarter?
- Read more: The Anatomy of a Data Breach: How Breaches Happen and Lessons Learned
Frequently Asked Questions
What is Ghostwriter’s main goal? Ghostwriter is a Belarus-aligned threat group that conducts cyber espionage and influence operations. Its primary goal appears to be supporting broader geopolitical objectives, which can include intelligence gathering and disruption of targeted governments.
How does the geofencing work in this attack? The geofencing in this attack means that the malicious PDF will only trigger the full attack chain if the victim’s IP address is located within Ukraine. If the victim is outside Ukraine, they receive a benign file, thus wasting no resources on non-target users.
Will this type of attack spread beyond Ukraine? While the current campaign is heavily focused on Ukraine due to geopolitical context, the techniques used—geofencing, host profiling, and advanced evasion—are highly transferable. It’s plausible these methods could be adapted for attacks targeting other regions or entities if strategically beneficial to the threat actor.