So, have you ever stopped to think about the sheer, unadulterated evolution of digital espionage? It’s not just about stealing data anymore; it’s about becoming a ghost in the machine, a persistent whisper that never fades. That’s precisely what the Russian outfit Secret Blizzard appears to have perfected with its long-running Kazuar backdoor, now rebranded into a modular, peer-to-peer (P2P) botnet. Think less clunky remote control, more a decentralized, insidious network that’s practically invisible.
These folks, tied to the Russian intelligence service (FSB) and often playing in the same sandbox as Turla, Uroburos, and Venomous Bear, aren’t new to this game. They’ve been kicking around since at least 2005, according to researchers, and their sights are firmly set on governments, diplomats, defense contractors, and critical infrastructure across Europe, Asia, and, you guessed it, Ukraine. Back in 2020, we saw them pop up targeting European governments, and three years later, Ukraine was in their crosshairs again. Kazuar isn’t some fly-by-night malware; it’s a seasoned, seasoned operative.
The ‘Leading’ Edge of Stealth
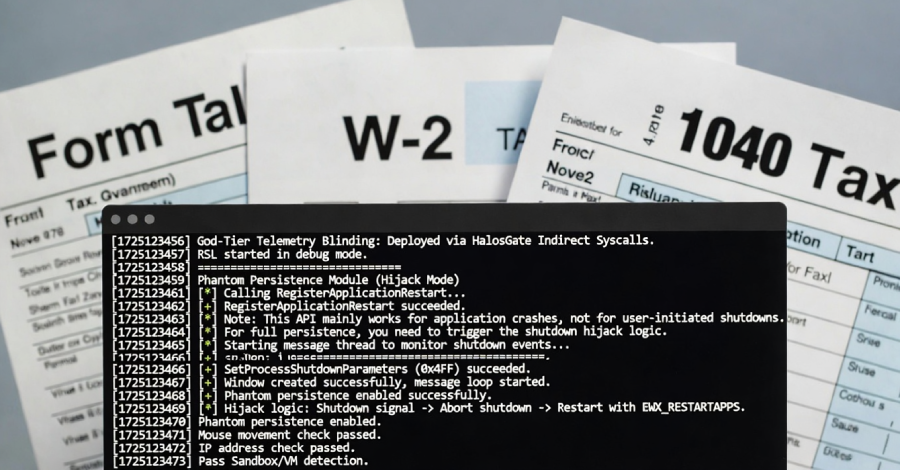
What’s truly interesting—and frankly, a bit chilling—is how Kazuar has been modularized. Microsoft’s deep dive reveals three distinct parts: the kernel, the bridge, and the worker. This isn’t your grandad’s botnet architecture.
The Kernel module. This is the brain. It’s the central dispatcher, coordinating everything, deciding who’s in charge, and ensuring the data flows where it needs to go without raising eyebrows. It elects a ‘leader’—basically, one infected machine that acts as the go-between for the shadowy command-and-control (C2) server. The other infected machines? They go dark. “Silent” mode, they call it. Less traffic, less noise, less chance of tripping an alarm.
“The Kernel leader is the one elected Kernel module that communicates with the Bridge module on behalf of the other Kernel modules, reducing visibility by avoiding large volumes of external traffic from multiple infected hosts.”
That leader election process is entirely internal, a digital popularity contest based on uptime and reboot cycles. It’s designed for resilience and stealth. The Bridge module, on the other hand, is the external face of this operation. It’s the proxy that talks to the C2, using standard protocols like HTTP, WebSockets, or even Exchange Web Services (EWS) – think things that normally happen on a corporate network. Inside, though, communications between modules are handled via inter-process communication (IPC) methods like Windows Messaging, Mailslots, and named pipes. It’s all AES-encrypted and serialized with Google Protocol Buffers. Blends right in.
And the Worker module? That’s the grunt work. Keylogging, screen capturing, digging through your files, poking around your network, snagging your emails (yes, even Outlook downloads), watching your windows, and scooping up any recent files. All the juicy intel is encrypted, stashed locally, and then, when the time is right, handed off to the Bridge for exfiltration.
Microsoft points out Kazuar’s sheer versatility. We’re talking about 150 configuration options here. Need to bypass certain security measures? Done. Want to schedule data theft for odd hours? Easy. Control how much data gets sent and when? A breeze. They’ve even baked in bypasses for AMSI, ETW, and WLDP. This thing is built to evade, to persist, and to extract whatever information Secret Blizzard deems politically important—documents, emails, the lot.
Why Does This Modular Approach Matter?
The real trick here, the bit that keeps security analysts up at night, is that modular, highly configurable nature. Sticking to signature-based detection for Kazuar is like bringing a water pistol to a wildfire. Microsoft’s advice? Focus on behavioral detection. Watch for anomalies, for processes doing things they shouldn’t be, rather than trying to catch a known bad file. Because with Kazuar, the ‘bad file’ can change its stripes faster than a chameleon on a disco floor.
This whole P2P evolution isn’t just a technical upgrade; it’s a philosophical shift in how these actors operate. They’re moving away from the centralized, easily identifiable C2 servers that have been the Achilles’ heel of botnets for years. By distributing control and communication across infected nodes, they make themselves exponentially harder to track and dismantle. Who controls the botnet when any infected node can become a commander? Who is actually making money when the network is so distributed? This is about long-term, low-and-slow espionage, designed to embed itself and extract value over months, if not years. It’s a stark reminder that the digital battlefield is constantly shifting, and staying ahead requires not just understanding the tools, but the intent behind them.
What Does This Mean for Defending Against Nation-State Actors?
The days of simply patching vulnerabilities and running antivirus are long gone, especially when dealing with actors like Secret Blizzard. Their shift to a modular, P2P architecture for Kazuar means that traditional defenses are increasingly inadequate. Companies need to invest heavily in advanced threat detection capabilities, focusing on behavioral analytics and network traffic analysis. Understanding the normal ‘noise’ of your network is paramount, so you can spot the subtle deviations that a sophisticated backdoor like Kazuar might introduce. It’s about building a detection system that’s as adaptable and multifaceted as the threats it’s designed to counter.
How is Kazuar Different from Older Botnets?
Older botnets often relied on a centralized C2 server that acted as a single point of failure. If that server was found and taken down, the entire botnet could be disrupted. Kazuar’s new P2P architecture decentralizes this control. Instead of a single command center, infected machines communicate with each other, electing leaders and sharing tasks. This makes the botnet far more resilient to takedowns, as there’s no single server to target. It’s a smarter, stealthier way to operate, allowing for longer-term persistence and more effective data exfiltration.
**
🧬 Related Insights
- Read more: React Server Components Hit by Critical DoS Flaw (CVE-2026-23870)
- Read more: Early ‘fast16’ Malware Foreshadowed Stuxnet’s Sabotage
Frequently Asked Questions**
What is the Kazuar backdoor? The Kazuar backdoor is a piece of malware used by Russian hacker groups for espionage. It has recently been evolved into a modular, peer-to-peer botnet for enhanced stealth and long-term data collection.
Who is behind the Kazuar botnet? The Russian hacker group Secret Blizzard, which is associated with the Russian intelligence service (FSB), is behind the development and deployment of the Kazuar botnet.
How does the P2P structure make Kazuar more dangerous? The peer-to-peer (P2P) structure makes Kazuar more dangerous by decentralizing its command and control. This means there isn’t a single server to target, making it much harder to detect and disrupt the botnet, allowing for prolonged periods of stealthy operation and data theft.