So, you’re a Ruby developer. You need a gem. A quick gem install whatever should be your digital equivalent of popping into the corner store. But lately, that quick trip has become a no-go. RubyGems.org, the place where all those essential little code building blocks live, has slammed the doors shut on new accounts. Why? Because hundreds of bad actors decided to flood the place with poison.
This isn’t some abstract security researcher’s nightmare; it’s a direct impediment to the daily grind of hundreds, if not thousands, of developers. The immediate impact isn’t that your existing gems are suddenly compromised – maintainers assure us that’s not the case. The real sting is the friction. Need to spin up a new project? Trying to onboard a new team member? Tough luck. The registration pipe is effectively capped.
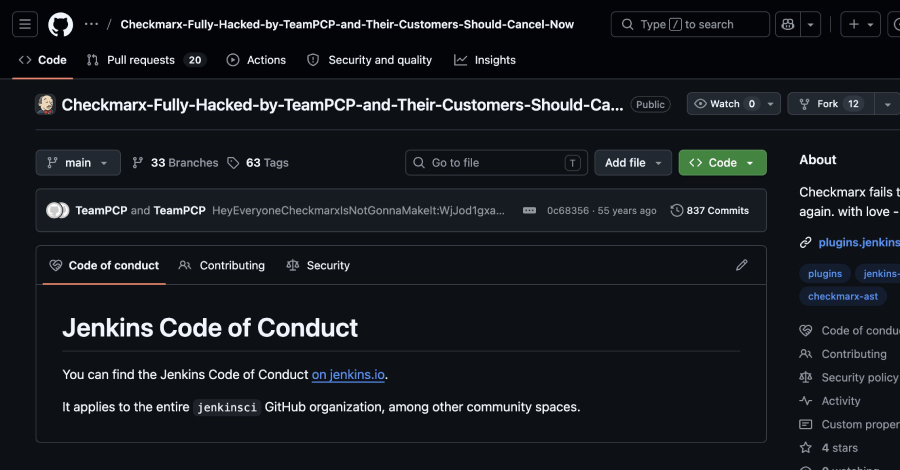
What we’re seeing here isn’t just a simple DDoS attack, despite what the initial communication might suggest. This was a targeted, high-volume spam operation. We’re talking bots, hundreds of them, churning out package after package, each designed to look legitimate while hiding… well, something nasty. It’s the digital equivalent of a thousand fake flyers plastered over a town square, designed not to inform, but to obscure and infect.
The immediate fallout for the average Ruby coder is inconvenience. The deeper implications, however, are far more chilling. This incident spotlights a systemic vulnerability within package registries – the very bedrock of modern software development. These repositories are the digital larder for developers, and when that larder is compromised, the whole house of cards can wobble.
Is This Just Bad Actors Being Bad Actors?
Look, it’s easy to dismiss this as just another headline about hackers. But the ‘how’ and ‘why’ here matter. This wasn’t a single sophisticated breach of a central server. Instead, threat actors exploited the registration process itself. They overwhelmed the system with spam, pushing malicious code under the guise of legitimate packages. RubyGems is talking about rate limiting and WAF (Web Application Firewall) protection – essential steps, certainly. But it feels a bit like building a better lock after the burglars have already rifled through your mail.
The security team’s note about the attackers attempting XSS and data exfiltration adds another layer. It suggests the initial spam campaign might have been a smokescreen—a distraction while they tried to pry open more sensitive systems or steal credentials. Maciej Mensfeld, a member of the RubyGems security team, voiced this concern starkly:
My worry with this RubyGems attack: it could be masking something more sophisticated. No proof, just a security researcher’s intuition. Hope I’m wrong.
That gut feeling, from someone on the inside, is worth more than any press release. It hints at a broader strategy than just petty mischief. It suggests a reconnaissance phase, a probing of defenses, all hidden within a seemingly mundane act of package submission.
This incident, unfortunately, isn’t an anomaly. We’ve seen similar patterns across various ecosystems. Log4j, PyPI, npm – they’ve all been targets. The attack vector is becoming depressingly familiar: compromise the trusted distribution channel, and you compromise everything that relies on it. The reliance on open-source libraries, while a massive boon for productivity, creates a single point of failure if not meticulously guarded.
What Does This Mean for You?
For individual developers, the immediate takeaway is a healthy dose of paranoia. Always check your dependencies. Understand what you’re pulling into your projects. For larger organizations, this is a flashing neon sign that your software supply chain security needs a serious audit. Relying on registries to do all the heavy lifting isn’t enough anymore. It’s about building multiple layers of defense, from static analysis to dependency vetting, and frankly, cultivating a culture where security isn’t an afterthought but a prerequisite.
The suspension is a temporary fix, a band-aid. The real work involves hardening the infrastructure, detecting anomalous behavior at the submission level, and perhaps, rethinking the very architecture of how these essential code repositories operate in a world where every digital doorway is a potential target. The developers who rely on RubyGems are waiting. And hoping that the digital equivalent of a town square cleanup happens swiftly, and more importantly, effectively.
This isn’t just about RubyGems; it’s about the underlying architecture of trust in the developer ecosystem. When that trust is eroded, even by temporary measures, the ripple effect is substantial. The real question isn’t if these registries are vulnerable, but how we build a more resilient foundation for the code that powers our digital lives. The hundreds of malicious packages are just the latest symptom of a deeper, more systemic illness.