The cursor blinked on a fresh vulnerability report, the kind I’ve seen a thousand times. Then the news dropped: Checkmarx, the company supposedly policing code, had its own Jenkins AST plugin fiddled with. Again.
Look, for twenty years I’ve watched Silicon Valley chase its own tail, rebranding old security holes with new buzzwords and charging a fortune to fix them. This latest shenanigan from TeamPCP, hitting Checkmarx’s Jenkins AST plugin just weeks after they messed with KICS and a slew of VS Code extensions, is less surprising and more… wearisome.
Checkmarx itself confirmed it. A compromised version of their plugin, which apparently lives on the esteemed Jenkins Marketplace (a place that often feels more like a dusty bazaar than a secure repository), was pushed out. They’re scrambling, telling folks to only use version 2.0.13-829-vc72453fa_1c16 from December 17, 2025. Yes, you read that date right. They’re living in the future with their security patches. Or, more likely, it’s a typo that underscores the chaos.
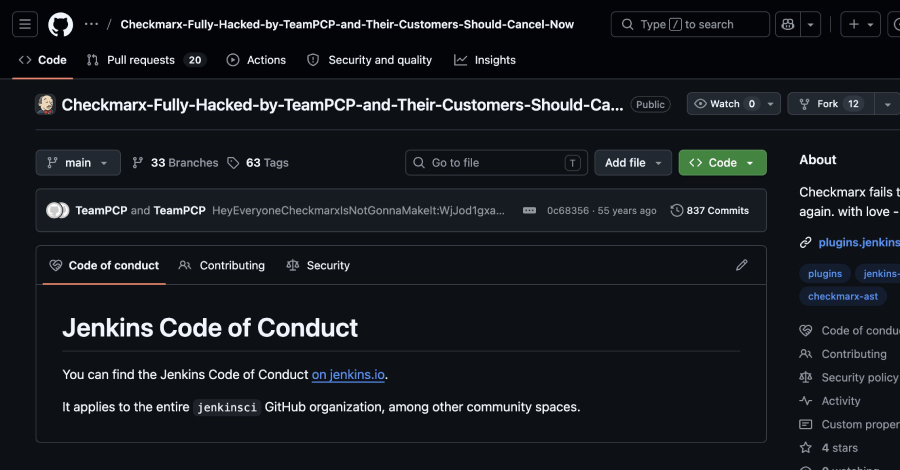
And the audacity. According to researchers Adnan Khan and SOCRadar, TeamPCP didn’t just sneak in; they defaced the GitHub repo. “Checkmarx-Fully-Hacked-by-TeamPCP-and-Their-Customers-Should-Cancel-Now.” The description? “Checkmarx fails to rotate secrets again. with love – TeamPCP.” Ouch. That’s not just a hack; that’s a public, digital spanking.
Who Is Actually Making Money Here?
This whole supply chain charade is a goldmine for some, and a recurring nightmare for everyone else. TeamPCP, whoever they are—nation-state, organized crime, bored teenagers with too much time and a VPN—they’re obviously profiting. But who else? The cybersecurity firms that then get hired to clean up the mess. The vendors who sell the next layer of “unbreakable” security that will inevitably be broken. It’s a perpetual motion machine of fear and revenue, and we, the users, are just the cogs.
Think about it. TeamPCP’s campaign since March 2026 has been a masterclass in exploiting the blind trust we place in our developer tools. They compromised KICS, then Bitwarden’s CLI, then VS Code extensions. Each step is a logical leap, leveraging the interconnectedness that makes modern development efficient but also terrifyingly fragile.
Did Checkmarx Actually Learn Anything?
The SOCRadar folks hit the nail on the head: “The fact that TeamPCP is back inside Checkmarx systems just weeks later points to one of two possibilities: either the initial remediation was incomplete and credentials were not fully rotated, or the group retained a foothold that wasn’t identified during the March response.” This isn’t rocket science; it’s basic hygiene. If you get robbed, you don’t leave the same window unlocked. Apparently, some software companies operate on a different playbook.
This isn’t about a specific bug. This is about trust. When a company like Checkmarx, whose product is literally about checking code, can’t secure its own development pipeline and its published plugins, where does that leave the rest of us?
“A second Checkmarx incident happening this soon suggests the group is actively watching for re-entry points, testing the depth of past remediations, and capitalizing on any gaps.”
That quote, folks, is the kicker. They’re not just opportunistic; they’re patient and analytical. They’re probing. And they’re finding weaknesses. The question isn’t if they’ll find more, but where and when.
I’ve seen vendors promise the moon and deliver… well, a slightly more polished crater. This feels like that. The industry needs to stop selling the illusion of perfect security and start talking about resilience, about detection, about rapid response when (not if) these inevitable compromises happen. Because they will happen. And right now, the attackers seem to be winning the trust game, one compromised plugin at a time.
What’s the End Game for TeamPCP?
While the immediate concern is about compromised tools and potential data exfiltration, the long-term strategy of groups like TeamPCP is a chilling thought. They’re not just stealing credentials; they’re sowing discord and eroding faith in the very systems developers rely on. The ultimate goal might be broader disruption, financial gain through targeted extortion, or even state-sponsored espionage disguised as petty crime.
Whatever their motives, the pattern is clear: exploit trust, gain access, propagate malware, and repeat. The latest Checkmarx incident is a stark reminder that no matter how sophisticated the security tools are, human error, lax practices, and the inherent risks of interconnected systems remain the weakest links. And groups like TeamPCP are exceptionally good at finding those links.
🧬 Related Insights
- Read more: Adobe Acrobat Zero-Day Active Since December—Users Exposed
- Read more: Storm-1175’s 24-Hour Ransomware Blitz: N-Days to Nightmare
Frequently Asked Questions
What does the Checkmarx Jenkins AST plugin do?
The Jenkins AST plugin is used to integrate Checkmarx’s Application Security Testing (AST) platform into the Jenkins CI/CD pipeline, allowing for automated code scanning and security analysis.
Will this attack affect my organization if I don’t use Checkmarx?
While your organization might not be directly affected if you don’t use the compromised plugin, the attack highlights the broader risks within the software supply chain. Dependencies on other libraries and tools could potentially expose you to similar threats.
How can I protect myself from supply chain attacks like this?
Practices like verifying software integrity, using trusted repositories, keeping all software updated, implementing strict access controls, and employing runtime security monitoring can help mitigate supply chain risks. For developers, it’s crucial to stay vigilant about the tools and libraries you integrate.