So, Checkmarx. Big name in app security testing. They’ve just had their Jenkins plugin — the one that’s supposed to find security holes — hijacked. Uploaded a poisoned version to the Jenkins Marketplace. Classic. This isn’t just a boo-boo; it’s a full-blown supply-chain attack. The usual suspects, TeamPCP, are crowing about it. They even left a nice little message: “Checkmarx fails to rotate secrets again.” Charming.
Jenkins. The workhorse of DevOps. Builds, tests, deploys. Your entire software lifecycle humming along. You trust it. Or you did. Now, a compromised plugin is slithering into those pipelines. The AST plugin. Supposed to be your digital watchdog. Instead, it’s now a wolf in sheep’s clothing, sniffing out credentials. A spokesperson confirmed the attackers got the keys from a previous Trivy supply-chain mess. Recycling? Apparently, so are the hackers.
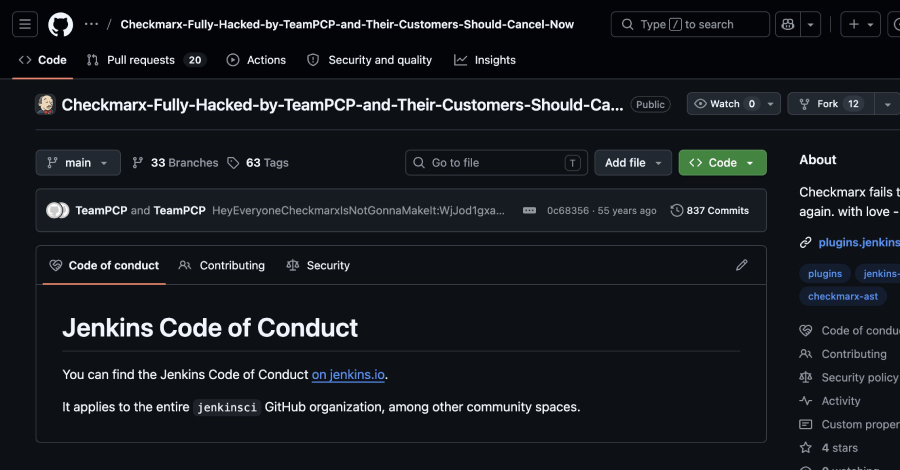
This is the third hit for Checkmarx since March. Third. Seems someone’s got a personal vendetta. Or maybe just a really efficient hacking operation. TeamPCP, using credentials pilfered from the Trivy breach, got into Checkmarx’s GitHub. Then, they just… tweaked the code. Dropped a malicious version of the Jenkins AST plugin. And not even subtly. The version number looks like it was typed by a toddler. No git tag. No GitHub release. Just a rogue file appearing out of nowhere.
The Grand Theft Auto of Developer Tools
It’s not just Jenkins. TeamPCP’s been busy. They’ve been pushing out backdoored versions of developer tools across GitHub, Docker, and VSCode. Stuff that sniffs out and steals your sensitive data. They kept access for at least a month. Long enough to poison the well. Then, in April, LAPSUS$ popped up with data from Checkmarx’s private GitHub. A veritable buffet of corporate insecurity.
Checkmarx is, of course, telling everyone to use version 2.0.13-829.vc72453fa_1c16, or older. Good luck finding that needle in the haystack of compromised versions. They assure us their GitHub is separate from customer data. We’ll take their word for it. For now. But if you downloaded the bad plugin? Assume your secrets are toast. Rotate everything. Look for the intruder. They’re probably already inside your network, waving hello.
This whole episode feels… familiar. Remember when SolarWinds happened? This is the same playbook. A trusted vendor compromised, its product weaponized, and the downstream effects rippling across countless organizations. The only difference? This isn’t a nation-state; it’s a group that seems to be enjoying the chaos. And Checkmarx, a company that sells security, is the latest victim. The irony is thicker than a stale corporate memo.
What’s the takeaway here? Relying on a single vendor for security, even a security vendor, is a gamble. And in the world of CI/CD, where every line of code is a potential vector, the stakes are astronomical. This isn’t just about a compromised plugin; it’s a stark reminder that the most sophisticated attacks often come from within the systems we’ve built to protect ourselves.
Why Does This Matter for My Pipeline?
The compromise of the Checkmarx Jenkins AST plugin is a direct threat to the integrity of your software development lifecycle. If an attacker can inject malicious code into a security tool, they can bypass your existing defenses and potentially gain unauthorized access to sensitive information or systems. This incident underscores the critical need for rigorous verification of all third-party components and plugins integrated into CI/CD pipelines.
A Pattern of Negligence?
TeamPCP’s smug message about Checkmarx failing to rotate secrets isn’t just a taunt; it points to a systemic issue. For a security firm, repeated compromises stemming from credential mismanagement are more than embarrassing – they’re a critical failure of fundamental security practices. This isn’t the first time a company has been targeted due to lax secrets management, and it won’t be the last, but for Checkmarx, it’s a particularly damaging indictment.
As a result of that access, the attackers were able to interact with Checkmarx’s GitHub environment and subsequently publish malicious code to certain artifacts.
This statement from Checkmarx, while factual, glosses over the severity. It’s not just ‘malicious code’; it’s a Trojan horse delivered through a channel designed for trust. The attack vector bypasses the usual security scans because it’s coming from a trusted source, or at least, a source that was trusted.
The continuous integration and continuous deployment (CI/CD) pipeline has become a prime target for attackers. Because it touches so many parts of the development process, a compromise here can have cascading effects. This Checkmarx Jenkins plugin incident is another nail in the coffin for the myth that CI/CD pipelines are inherently secure. They’re only as secure as the weakest link, and in this case, that link was a compromised tool meant to find weaknesses.