
Interpol's Cyber Sweep: 13 Nations, Modest Takedowns
Interpol's Operation Ramz wrapped up, uniting 13 Middle Eastern nations against cybercrime. The takedown numbers might be small, but the cross-border cooperation is a significant shift.
Microsoft's Digital Crimes Unit has severed a critical artery in the cybercrime underworld, dismantling a sophisticated malware-signing-as-a-service operation. This isn't just about shutting down a website; it's about understanding the architectural shifts enabling the weaponization of trust.

Interpol's Operation Ramz wrapped up, uniting 13 Middle Eastern nations against cybercrime. The takedown numbers might be small, but the cross-border cooperation is a significant shift.
A new Windows zero-day, dubbed YellowKey, is exposing BitLocker-protected drives. Microsoft has released emergency mitigations, but public exploits are already circulating.

Your AI morning briefing for May 20, 2026 — the top stories you need to know.

Another week, another handful of zero-days hitting Windows. Microsoft's patching efforts are starting to look like a game of whack-a-mole.

A significant operation enabling cybercriminals to digitally sign malware as if it were legitimate software has been dismantled. This attack vector highlights how even trusted cloud services can be subverted, impacting user trust and system security.
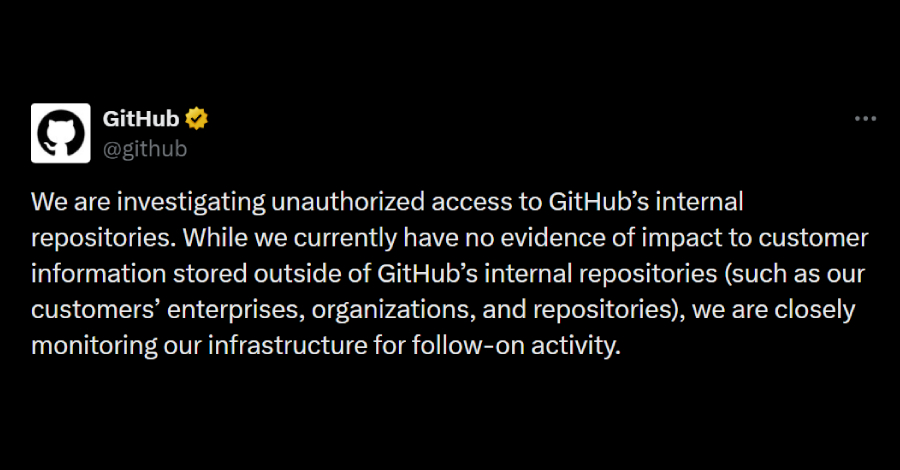
GitHub's internal source code is reportedly up for grabs on the dark web, and the company's scrambling to figure out what happened. This latest incident highlights the ever-present danger lurking in the supply chain.

A max-severity flaw is leaving AI applications built with ChromaDB wide open to hijacking. Imagine your carefully crafted AI assistant suddenly spouting gibberish – or worse.

Ever wonder why that antivirus scan takes *forever*? Turns out, a clever trick with Windows file paths might be the culprit, letting attackers hide in plain sight. Welcome to GhostTree.

Android users were unwittingly ensnared by Trapdoor, a massive ad fraud scheme. This operation masqueraded as utility apps, spiraling into millions of fraudulent ad requests daily.

A months-long breach at NYC Health + Hospitals has compromised the data of 1.8 million people, exposing everything from medical histories to biometric identifiers.

Ever wonder how malware slips past your defenses, looking utterly legitimate? It turns out there's a whole underground industry dedicated to giving it a convincing digital handshake. Fox Tempest, a cybercrime-as-a-service provider, was just busted for doing exactly that, and the implications are chilling.
Boardrooms fret about data security, and rightly so. Varonis says its new platform fixes it. We're not so sure.




