
Windows Update Failures Hit Restricted Networks [2026]
Restricted Windows networks are facing update failures after January's non-security preview. Microsoft's workaround is here, but it highlights ongoing network update woes.
Microsoft's Digital Crimes Unit has severed a critical artery in the cybercrime underworld, dismantling a sophisticated malware-signing-as-a-service operation. This isn't just about shutting down a website; it's about understanding the architectural shifts enabling the weaponization of trust.

Restricted Windows networks are facing update failures after January's non-security preview. Microsoft's workaround is here, but it highlights ongoing network update woes.
The deluge of alerts facing IT teams isn't the problem; it's the manual slog through disparate systems that cripples incident response. A new webinar aims to shed light on these hidden bottlenecks.

Forget incremental updates. SEPPMail Secure E-Mail Gateway just dropped a bomb, revealing a cascade of vulnerabilities that could let attackers not just peek, but take the keys to your entire email kingdom. We're talking remote code execution and unfettered access to every message flowing through your enterprise. This isn't just a patch; it's a seismic shift in how we need to think about email gateway security.
They say developers are paranoid. Turns out, they're right. A popular VS Code extension, Nx Console, just became the latest vector for a sophisticated credential stealer.
Universal Robots' cobots are no longer safe from a critical vulnerability. A flaw in their PolyScope operating system could let attackers seize control of entire robot fleets.

Your AI morning briefing for May 19, 2026 — the top stories you need to know.

Your employees are likely using AI tools IT doesn't know about. This isn't just a security headache; it's an architectural blind spot that needs immediate attention.

Forget malware. A sophisticated actor named Storm-2949 just proved that compromising a single cloud identity can unlock the entire kingdom. Microsoft's latest report lays bare a meticulously orchestrated breach that went from a stolen password to a full-blown cloud infrastructure takedown.

A potent zero-day exploit is currently tearing through Microsoft Exchange servers, leaving businesses exposed. This isn't just an IT problem; it's a direct threat to your sensitive communications.
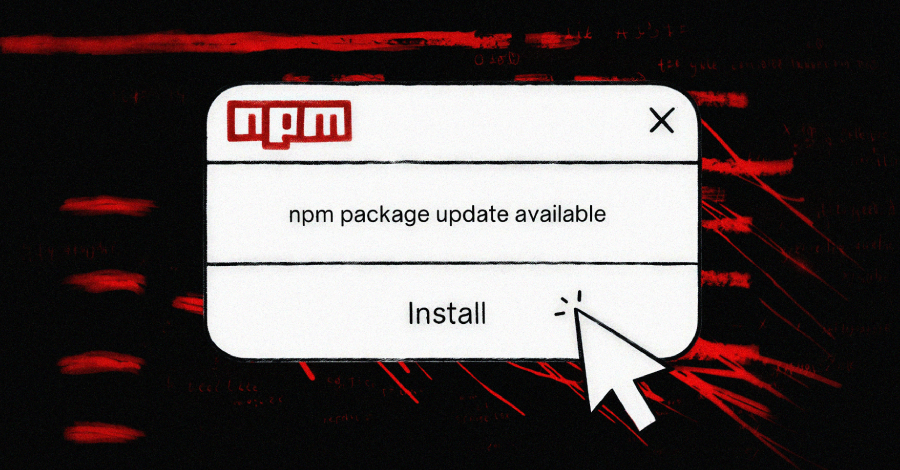
The digital equivalent of finding a Trojan horse in your code library just got a lot scarier. The Mini Shai-Hulud campaign is here, and it's not just about hitting tech giants; it's about every developer and every organization that relies on open-source software.
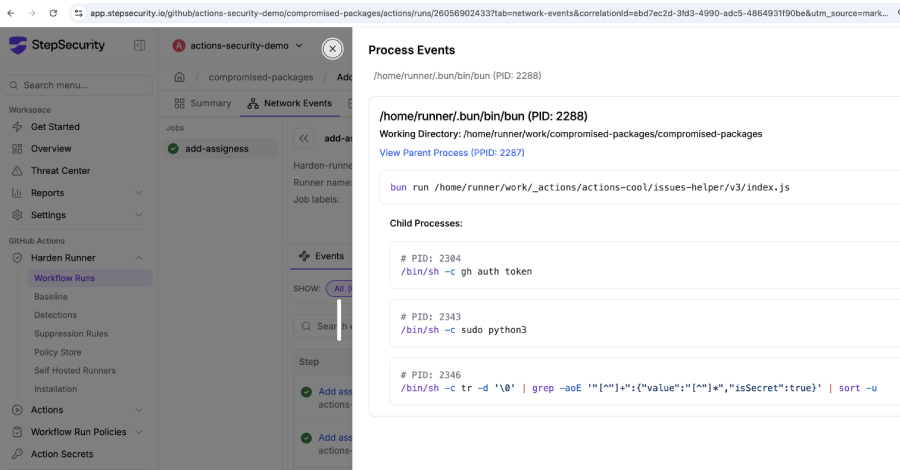
Forget the fancy code; the real news is that the tools you trust to build your software might now be the ones stealing your secrets. A clever hijacking of popular GitHub Actions means your CI/CD pipelines could be quietly coughing up credentials.

A leaked malware strain is now fueling a fresh wave of attacks against the Node Package Manager. Developers' secrets and systems are increasingly at risk.




