Facebook accounts pilfered. This isn’t new. But how? Via Google. Yes, that Google. The same company peddling AI that might soon write your emails for you.
Researchers have stumbled upon a rather audacious phishing campaign. It’s not just slinging emails into spam folders. No, this one’s far more insidious. It’s worming its way through Google’s trusted infrastructure, specifically using Google AppSheet. The result? Tens of thousands of Facebook accounts – mostly business and advertiser profiles – are being snatched. Why target businesses? Simple. They have money. They have reach. And criminals want to monetize that.
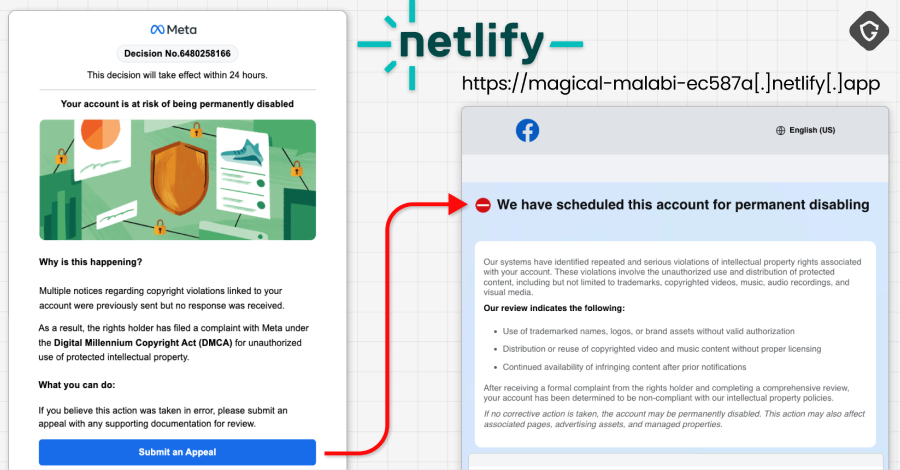
The trick is deceptively simple. Attackers are leveraging Google AppSheet, a tool designed for building apps without coding. It’s meant for legitimate notifications, workflow automation, that sort of thing. But phishers can customize the sender name. They make it look like it’s coming from [email protected], routed through appsheet.bounces.google.com. To the average user, it screams legitimacy. Especially when the content mentions Facebook policy violations or copyright complaints. Who questions Google directly?
This isn’t some lone wolf operation. It’s a Vietnamese-linked crew. They’ve already snagged around 30,000 accounts. And they’re still at it. The prize? Business pages, ad accounts, anything that makes Facebook a revenue generator. Once inside, they run scams, push fraudulent ads, or worse, sell the access. Some even have the nerve to offer “account recovery” services for the very mess they created. The audacity is almost impressive. Almost.
The stolen accounts are mostly pages and business profiles that have financial value: advertising accounts, brand pages, and companies that rely on Facebook for marketing.
The whole charade leads to one place: credential harvesting. Facebook login details, two-factor authentication codes, recovery data – they want it all. This isn’t just a bad email; it’s a whole industrial setup. Think Telegram bots and channels diligently processing stolen data. It’s a grim proof to how easily trust in major platforms can be exploited.
Is Trust in Google Broken?
This campaign highlights a broader, more unsettling trend. We, as users, place an enormous amount of faith in established tech giants. When an email lands with a google.com domain, our guard drops. We assume it’s safe. This operation weaponizes that assumption. It’s a stark reminder that even the most trusted conduits can be corrupted. The attackers aren’t breaking into Facebook’s systems directly; they’re tricking users through a platform we implicitly trust to be secure.
Facebook itself doesn’t send urgent account warnings through Google. Shocking, I know. If you get a frantic message about your account, especially with a 24-hour deadline, don’t click. Go directly to Facebook. Don’t trust the link. And if a form asks for your password, 2FA codes, DOB, phone number, and ID photos all at once? Run. That’s the full package criminals crave to completely hijack your digital life.
Security is the usual litany: enable 2FA, set up login alerts. Basic hygiene, really. But the real lesson here is vigilance. Question the source, even when it wears a familiar, trusted logo. The attackers prey on our complacency.
And for those who find themselves perpetually battling these digital pests, tools like Malwarebytes Scam Guard are apparently available. They even claim to work on AI chat platforms. Fascinating. Another layer of defense for an increasingly layered threat landscape.
Why Does This Matter for Businesses?
For businesses, the stakes are astronomical. Losing a Facebook business account isn’t just an inconvenience; it’s a direct hit to their marketing, their customer engagement, their bottom line. Imagine your primary sales channel suddenly controlled by a scammer. They could run malicious ads directing customers to fake sites, damaging your brand reputation and financial stability. Or they could simply hold your account hostage, demanding a ransom. This isn’t a hypothetical. It’s the current reality for many who rely on social media for their livelihood. This exploit underscores the critical need for strong internal security protocols and continuous employee training on recognizing sophisticated phishing attempts, regardless of the perceived legitimacy of the sender’s platform.
🧬 Related Insights
- Read more: Drift Protocol’s $280M Governance Hijack Exposes DeFi’s Multisig Weak Spot
- Read more: CVE-2026-3055: Citrix NetScaler’s SAML Memory Leak Goes Wild, Echoing CitrixBleed Nightmare
Frequently Asked Questions
What exactly is Google AppSheet? Google AppSheet is a no-code development platform that allows users to build mobile and web applications. It’s often used for automating workflows and sending notifications. In this case, it was misused by attackers to send convincing phishing emails.
Will my personal Facebook account be targeted? This particular campaign primarily targets business and advertiser Facebook accounts, which often have more direct financial ties and higher perceived value for attackers. While personal accounts can also be targeted by phishing, this operation’s focus is on monetizing commercial entities.
How can I protect myself from similar attacks? Always be skeptical of urgent messages, especially those demanding immediate action or personal information. Never click on links in suspicious emails; navigate directly to the platform’s official website or app. Enable two-factor authentication (2FA) and review your account’s security settings regularly. Report any suspicious activity to the platform immediately.