It’s not just about brute force anymore.
Imagine this: your prized shipment, a container full of high-value electronics, is supposed to be on a freighter steaming towards Rotterdam. Instead, a few keystrokes by a shadowy syndicate somewhere on the globe have subtly, almost invisibly, rerouted it. Not to another port, mind you, but straight into a waiting network of illicit warehouses. This isn’t science fiction; this is the bleeding edge of cargo theft, and it’s powered by the same digital tendrils that manage our every online transaction.
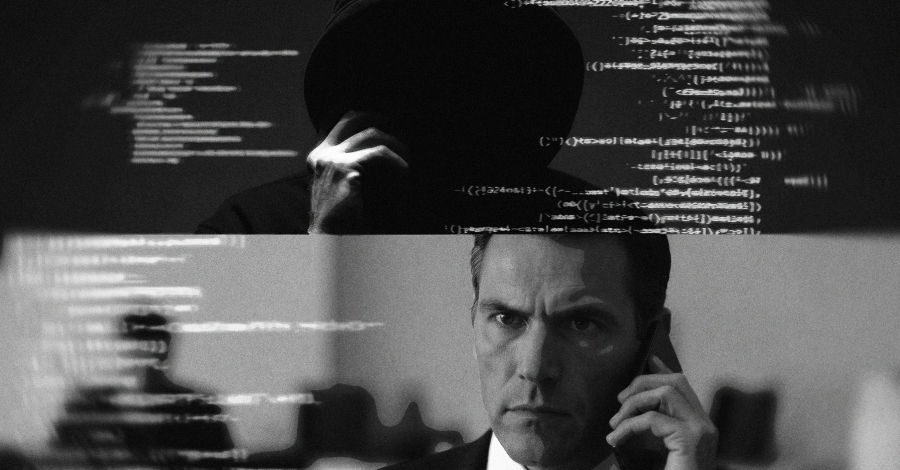
For years, cargo theft conjured images of masked figures disabling GPS trackers or audacious heists at dimly lit truck stops. That was the analog age of larceny. We’re now hurtling into the digital era, where the lock on the trailer door is far less important than the lock on the database that controls its destination. These aren’t your neighborhood bandits; they’re transnational syndicates, leveraging sophisticated cyberattack techniques to gain access to vital supply chain systems.
Think of it like this: instead of picking the physical lock on a bank vault, these criminals are now digitally cracking the vault’s security codes from their laptops. They aren’t interested in a single truck; they’re interested in orchestrating the disappearance of entire shipments, manipulating the digital breadcrumbs that guide goods across continents.
Why Is This Happening Now?
The world’s supply chains are incredibly complex, a sprawling digital nervous system connecting manufacturers, carriers, ports, and retailers. While this interconnectedness offers incredible efficiency, it also creates a vast attack surface. Each login, each data transfer, each piece of software used to track and manage freight is a potential entry point for attackers. Cybercriminals, ever the opportunists, have recognized this and are pivoting from purely digital targets to those that offer tangible, high-value assets accessible through compromised digital systems.
It’s a fascinating, albeit terrifying, evolution. The traditional silos of physical crime and cybercrime are not just blurring; they’re merging into a hybrid threat that’s far more insidious than either entity was alone. They’re using cyber means to achieve physical ends.
Cargo theft is no longer about small groups of criminals operating on the ground, but transnational cybercriminal syndicates using access to supply chain systems to reroute goods.
This quote from the initial report is chillingly accurate. It paints a picture of an organized, globally-minded criminal enterprise, not just a collection of individuals. This shift implies a level of coordination and resourcefulness that demands a commensurate upgrade in our defenses.
How Are They Doing It?
Phishing attacks that snag credentials, exploiting vulnerabilities in unpatched software used by logistics companies, or even social engineering to trick employees into granting access – the methods are varied and constantly evolving. Once inside a supply chain management system, the damage can be profound. They can alter manifests, change delivery instructions, or simply erase a shipment’s digital trail, making it vanish into the ether, only to reappear on the black market.
This isn’t just about lost goods; it’s about the erosion of trust in the very systems that keep our global economy moving. If we can’t rely on the digital assurances of where our goods are and where they’re going, the entire edifice of modern commerce begins to wobble. It’s a stark reminder that the digital and physical worlds are inextricably linked, and vulnerabilities in one inevitably bleed into the other.
What Does This Mean for the Future?
This trend signals a critical need for enhanced cybersecurity measures specifically tailored to supply chain operations. Companies can no longer afford to view IT security and physical security as separate domains. They must be integrated, with strong authentication, continuous monitoring, and proactive threat hunting becoming standard operating procedure. It’s like upgrading from a simple padlock on your front door to a full-scale biometric security system that monitors every movement – only this time, the ‘door’ is a digital portal into a global network.
The implications extend beyond immediate financial loss. Reputational damage, disrupted production lines, and even national security concerns can arise when critical supply chains are compromised. This isn’t just a problem for shipping companies; it’s a problem for manufacturers, retailers, and ultimately, consumers who rely on the timely and secure delivery of goods.
🧬 Related Insights
- Read more: Code Cowboys: 73 Fake VS Code Extensions Hijacked by GlassWorm v2
- Read more: 80,000 Hikvision Cameras Exposed: Cybercriminals Auction Off Access
Frequently Asked Questions
What kind of cargo is most at risk? Any high-value cargo, from electronics and pharmaceuticals to consumer goods and raw materials, is a prime target. The key is accessibility through cyber means.
Is my company safe from this type of threat? No company with digital supply chain dependencies is entirely safe. Proactive cybersecurity, vendor risk management, and employee training are essential.
How can businesses protect themselves? Implementing multi-factor authentication, regularly patching software, conducting security audits of third-party vendors, and investing in specialized supply chain security solutions are critical steps.