New TON trick.
That’s the short, and frankly terrifying, version. Researchers have spotted a fresh wave of the TrickMo Android banking trojan, and it’s not just after your one-time passwords anymore. This latest iteration, observed between January and February 2026, is turning infected devices into sophisticated network tools. Think less ‘grab your cash,’ more ‘become a silent infiltrator.’ France, Italy, and Austria are currently in the crosshairs. Lovely.
Network Pivots. That’s the headline here. ThreatFabric, the outfit that spotted this mess, says the updated module now includes reconnaissance, SSH tunneling, and SOCKS5 proxying. This allows compromised phones to act as programmable network pivots and traffic-exit nodes. They’re not just stealing data; they’re using your device to launch other attacks, hop internal networks, and mask their own digital fingerprints. It’s a significant escalation from the credential-snatching days.
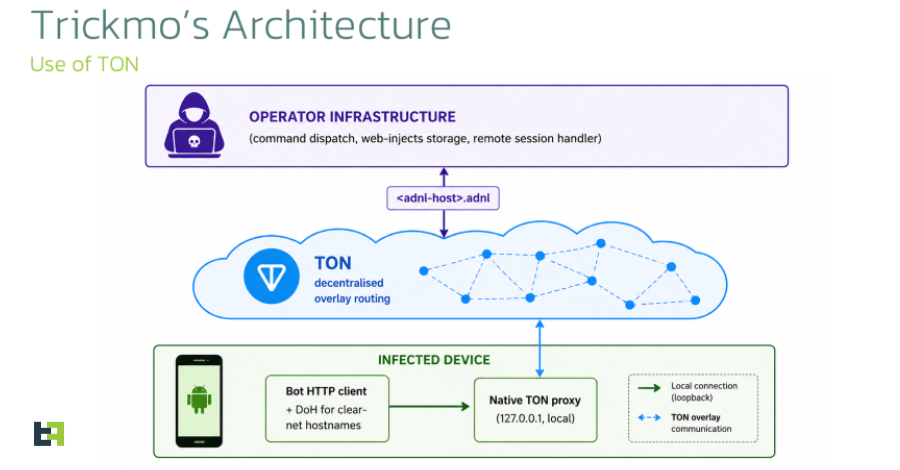
TrickMo itself isn’t exactly a spring chicken. It’s been around since late 2019, initially known for its ability to abuse Android’s accessibility services to swipe OTPs. It’s a seasoned pro at remote control – screen recording, keystroke logging, SMS interception, the works. But this new variant, dubbed TrickMo C, is architecturally different. Distribution happens via those shady phasing websites and dropper apps, which then pull down the actual malicious payload. The sneaky bit? The command-and-control (C2) infrastructure is now housed on The Open Network (TON) blockchain.
Why TON? Stealth, obviously. The malware has a built-in TON proxy. All those outbound C2 requests? They’re routed through this proxy, hitting .adnl hostnames, and resolved via the TON overlay. This makes it devilishly hard to track and shut down using traditional methods. Forget blocking IPs or domains; the traffic blends in with legitimate TON activity. It’s like trying to find a needle in a blockchain haystack.
“Instead of relying on conventional DNS and public internet infrastructure, the malware communicates through .adnl endpoints routed via an embedded local TON proxy, reducing the effectiveness of traditional takedown and network-blocking efforts while making the traffic blend with legitimate TON activity.”
And the dropper apps? They’re a masterclass in social engineering, masquerading as adult versions of TikTok. The malware itself? It plays dress-up as Google Play Services. Because who suspects Google?
The network-subsidiency is the real upgrade. Previous versions used Socket.IO for remote control. This new one equips attackers with what ThreatFabric calls a “remote shell-equivalent.” They can run commands like curl, dnslookup, ping, telnet, and traceroute from the victim’s network position. Imagine an attacker running ping inside your corporate network, originating from your phone. It’s an insider threat, powered by an outsider.
And that SOCKS5 proxy? It turns your phone into a discreet exit node. Malicious traffic goes out from your IP address. This is a direct blow to fraud detection systems used by banks, e-commerce sites, and crypto exchanges. They look for suspicious IPs; they’ll just see your phone. Brilliant for them, terrifying for you.
There are also a couple of dormant features for Pine hooking and NFC permissions. Not implemented yet, but it signals future expansion. These developers aren’t resting on their laurels; they’re actively planning the next phase of their digital crime spree.
Is This the End of Traditional Mobile Malware?
Maybe not the end, but certainly a significant evolution. We’ve seen banking trojans before, but the pivot to using devices as sophisticated network infrastructure, powered by decentralized tech like TON, is a new frontier. It blurs the lines between device compromise and network intrusion. Attackers are not just stealing data; they’re building networks of compromised devices that act as extensions of their own infrastructure. This requires a fundamental rethink of how we defend against mobile threats. It’s no longer just about securing the device itself; it’s about understanding how that device can be weaponized against the networks it connects to.
Why Does This Matter for Developers?
Developers, especially those working on applications that handle sensitive data or connect to internal networks, need to be acutely aware of these evolving threats. The ability of malware to act as a network pivot means that even if your application is perfectly coded, a compromised device running it can become a backdoor. Think about how your apps handle network requests, DNS lookups, and permissions. The inclusion of tools like SSH tunneling and SOCKS5 proxying suggests that attackers are actively looking for ways to traverse networks using compromised devices. This necessitates more strong network segmentation, stricter access controls, and continuous monitoring of network traffic, even if it originates from a seemingly trusted endpoint – your user’s phone.
TrickMo’s move to TON is a masterstroke of evasion. It sidesteps traditional takedowns. The capabilities it now wields turn a stolen phone into a powerful, untraceable attack platform. This isn’t just about banking trojans anymore. This is about advanced persistent threats, executed with consumer hardware.
🧬 Related Insights
- Read more: Rituals Data Breach: 41M Loyalty Members at Risk
- Read more: CVE-2026-20929: Hackers Hijack Your Certs with DNS CNAME Tricks
Frequently Asked Questions
What does TrickMo do? TrickMo is an Android banking trojan that has evolved to turn infected devices into programmable network pivots and traffic-exit nodes, using TON for command-and-control. It can steal credentials, record screens, and facilitate network reconnaissance.
How is this new TrickMo variant different? The latest variant uses The Open Network (TON) blockchain for stealthy C2 communications and incorporates SOCKS5 proxying and SSH tunneling, transforming compromised devices into network tools for attackers rather than just data thieves.
Can TON be used for legitimate purposes? Yes, TON is a decentralized blockchain that can be used for various applications, including secure messaging, file storage, and payments. However, in this context, malware is exploiting its infrastructure for malicious C2 communications.