Nearly 4,000 attacks. Four thousand. Targeting a single vulnerability. That’s CVE-2026-41940, a gaping hole in cPanel and WHM’s login flow. This isn’t some theoretical exploit; it’s live, it’s broad, and it’s dangerous. WatchTowr Labs found it. Imperva is now touting its own protections. But let’s cut through the PR.
This isn’t your average bug.
CVE-2026-41940 sits at a CVSS score of 9.8. A missing authentication for a critical function, according to the Common Vulnerability Scoring System. That means unauthenticated remote attackers can waltz right in. No phishing. No social engineering. Just a few well-crafted packets and they’re in your hosting control panel. And remember, WHM is the keys to the kingdom for server admins. cPanel is for the individual accounts. This flaw hits both. It’s tied to how sessions are loaded and saved. A classic, and terrifyingly simple, mistake.
The Wild West of Exploitation
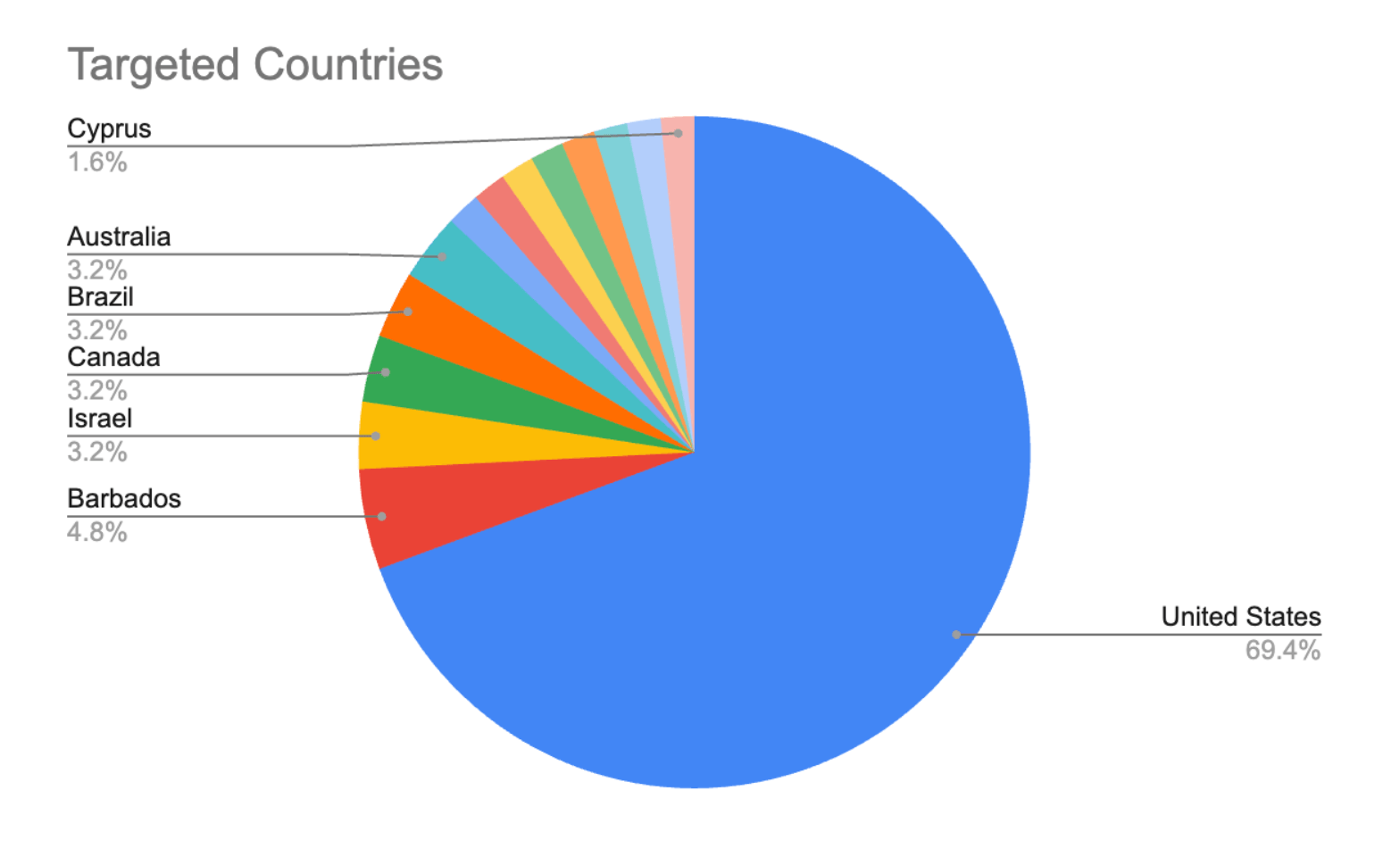
What’s truly telling is the spread. Imperva spotted attacks hitting sites across 15 industries and 17 countries. This isn’t targeted warfare. It’s a botnet sweeping the internet, looking for any vulnerable cPanel/WHM instance. The US caught the brunt of it, a predictable consequence of its massive hosting infrastructure. But Barbados and Israel? That’s just automated discovery at work. Attackers are casting a wide net, and if you’re running cPanel or WHM and haven’t patched, you’re in the net.
The most popular targets? Business, Society, and Education. Makes sense. These sectors are riddled with public-facing websites and distributed web infrastructure. They rely on control panels like cPanel/WHM. They’re also sectors that, frankly, might not always have the nimblest security teams.
“While observed volume remains limited compared to mass exploitation campaigns, the spread across industries and countries shows active probing for exposed cPanel and WHM instances.”
Limited? Perhaps. But the volume is growing, and the potential impact is astronomical. A 9.8 CVSS score doesn’t just happen. It signifies a flaw with severe consequences.
Imperva’s White Knight Moment?
So, Imperva rolls out its disclaimer: Imperva customers are protected out-of-the-box against CVE-2026-41940. Fantastic. For them, at least. Their Cloud WAF and WAF Gateway are apparently sniffing out the malicious patterns before they hit the vulnerable servers. Automatic protection for Cloud WAF users. Manual mitigation for WAF Gateway. It’s good to know that some portion of the internet is breathing easier.
But this brings us back to a familiar, and frankly, annoying, pattern in the cybersecurity world. Vendors selling protection after a vulnerability is known and actively exploited. It’s a race against time, and frankly, it’s a business model that profits from chaos. We saw this with Log4j. We see it constantly. The vendors get their press releases, the users get their invoices, and the attackers… well, they keep finding new holes.
Is This Just Another Log4j Moment?
Not quite. Log4j was a library. It was buried deep in countless applications. This is a control panel. A surface-level administrative tool. The difference is significant. Exploiting Log4j required deeper technical knowledge and integration. Exploiting CVE-2026-41940 is about hitting an exposed endpoint. The barrier to entry is considerably lower. That means more attackers, more botnets, and a higher likelihood of widespread compromise.
Why Does cPanel/WHM Need Better Security?
Because it’s everywhere. cPanel and WHM are stalwarts in the web hosting industry. Millions of websites run on servers managed by these tools. When a vulnerability like this emerges, it’s not a niche problem. It’s a global one. The ease of exploitation, combined with the sheer number of installations, makes it a prime target. Attackers aren’t interested in subtlety here; they’re interested in broad access. And these control panels are the direct path.
The Fix is Simple, the Urgency is Not
CPanel itself has released patched versions. The advice is unequivocal: update. Immediately. Verify your build. Restart the service. If you absolutely cannot patch, cPanel suggests blocking inbound traffic on ports 2083, 2087, 2095, and 2096. Or, you know, just stop the affected services. It’s not rocket science, but it requires administrative will and swift action.
But here’s the kicker: even if you patch, cPanel suggests purging affected sessions, forcing password resets, and checking for persistence mechanisms if you find any sign of compromise. This isn’t just about plugging a leak; it’s about cleaning up the mess the leak made. And that requires diligence.
This vulnerability is a stark reminder. The internet is a vast, interconnected beast. And too many administrators are still treating their control panels like a locked bedroom door when they should be fortifying a castle gate. The attackers aren’t waiting for you to get around to it. They’re already at the gates, and thanks to CVE-2026-41940, they might just be walking right in.
🧬 Related Insights
- Read more: Microsoft Dynamics Redirects Fuel Phishing at Scale [2026]
- Read more: Kimwolf Botnet’s Accidental I2P Siege: A Sybil Flood Exposes Anonymity’s Fragile Core
Frequently Asked Questions
What is CVE-2026-41940?
CVE-2026-41940 is a critical authentication bypass vulnerability in cPanel & WHM versions after 11.40. It allows unauthenticated attackers to gain unauthorized access to the control panel.
Are Imperva customers protected from this vulnerability?
Yes, Imperva states its Cloud WAF and WAF Gateway customers are protected against exploitation techniques associated with CVE-2026-41940.
What should I do if I use cPanel & WHM?
Administrators should immediately update to a patched version of cPanel & WHM, verify their build, and restart the service. If immediate patching isn’t possible, block specific ports or stop affected services.