Linux Under Siege.
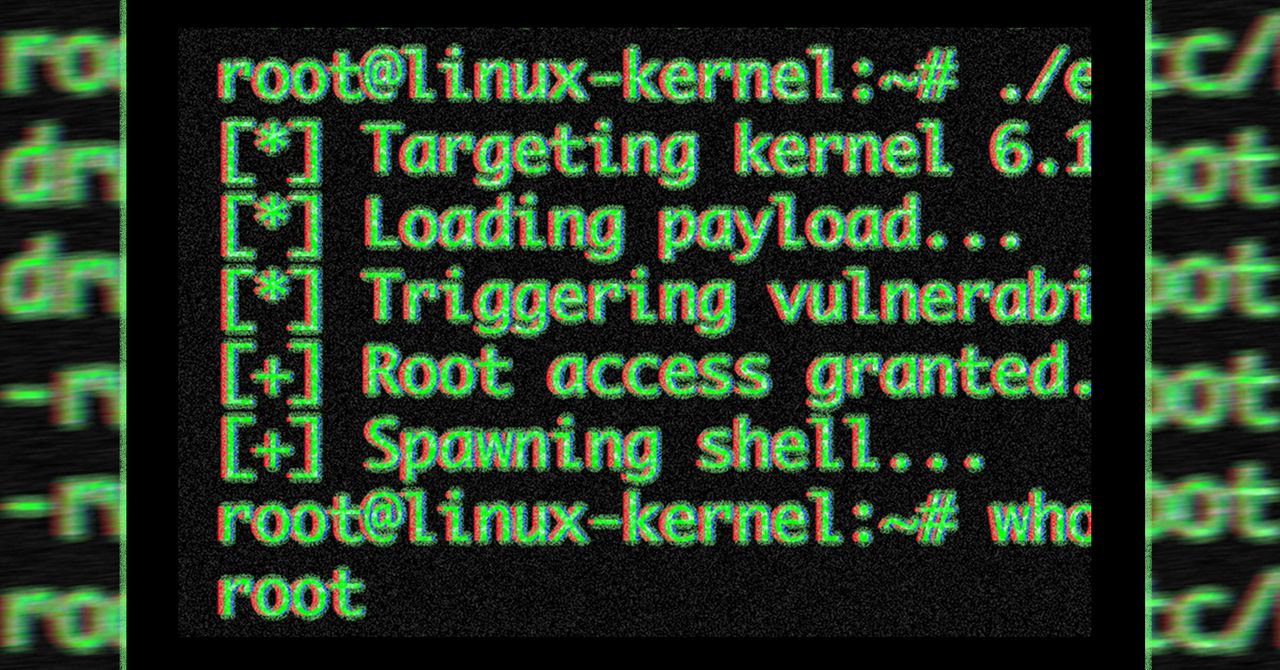
Forget your fancy firewalls. A public exploit for a nasty Linux bug just dropped. It hands attackers root access. Think data centers, your server, maybe even your personal rig. Alarms are blaring. Defenders are scrambling. It’s a mess.
This isn’t some theoretical whisper. Researchers from Theori released the exploit code Wednesday. Five weeks ago, they tipped off the Linux kernel team. Patches exist for a handful of versions. But most Linux distros? Still exposed. The exploit arrived before the fixes.
The ‘CopyFail’ Catastrophe
This critical flaw? CVE-2026-31431, nicknamed CopyFail. It’s a local privilege escalation. Boring tech term, right? It means someone who’s already on your system, even with zero permissions, can become the king. Root. Full stop.
And this one’s a doozy. A single script. No modifications needed. Works across the board. This isn’t just about one server. It’s about shared infrastructure. Kubernetes containers? Blasted wide open. Multi-tenant systems? Ripped apart. Even CI/CD pipelines, that sacred ground for developers, are vulnerable. An attacker lands on a vulnerable system – say, through a hacked WordPress plugin – runs this script, and BAM. They’re root. Every other tenant on that host? Fair game. The exploit doesn’t get them in, it just makes what happens after they’re in terrifyingly easy.
“Local privilege escalation” sounds dry, so let me unpack it. It means: An attacker who already has some way to run code on the machine, even as the most boring unprivileged user, can promote themselves to root. From there they can read every file, install backdoors, watch every process, and pivot to other systems.
This isn’t some probabilistic race condition. This is straight-line logic. The kernel’s crypto API has a flaw. A simple mistake. The ‘copy’ operation doesn’t actually copy data when it should. It writes outside the intended buffer. Like scribbling on the wallpaper outside the designated picture frame. Theori explains it: “The ‘copy’ of the AAD ESN bytes ‘fails’ to stay inside the destination buffer.” Simple. Devastating.
Is This the Worst Linux Exploit Ever?
Some seasoned security pros are calling it the “worst make-me-root vulnerabilities in the kernel in recent times.” High praise. They’re comparing it to Dirty Pipe (2022) and Dirty Cow (2016). Both were actively exploited. Those were bad. This might be worse.
Here’s the kicker. Linux distributors love to stick with older kernel versions. They backport fixes. It’s a familiar dance. But this time? Theori didn’t seem to coordinate with the distributors before going public. It’s effectively a zero-day. Or, as some are calling it, a “zero-day patch gap.”
Will Dormann, a senior analyst at Tharros Labs, didn’t pull punches. He called the coordination a “terrible job.” His point? Theori listed affected vendors. They told readers to apply vendor patches. But they never checked if those vendors actually had patches. None did. Mind-boggling, isn’t it?
Trying to get a comment from Theori? Tough luck. Attempts to reach them were unsuccessful. Meanwhile, distributions like Arch Linux, which did patch the vulnerability, are the lucky ones. The rest? Praying an attacker doesn’t find them first.
This isn’t just a technical problem. It’s a coordination failure. A public disclosure before a widespread fix. It leaves the digital world exposed. For anyone running Linux, especially in a shared environment, the next few weeks are going to be a nail-biter. Patching is paramount. But the damage might already be done. The exploit is out. The cat’s out of the bag, and it’s already a root user.