Cybercrime goes freight.
Look, we’re all used to the terrifying dance of ransomware gangs. Stolen credentials, creeping persistence, network recon, the big payday. It’s a well-trodden path, mapped out in attack frameworks and kill chains. But what if I told you that same dark playbook is now being hijacked, not for digital gold, but for… well, actual physical cargo? We’re talking about entire truckloads of goods, vanishing from the legitimate supply chain and reappearing on the black market. Bottled water, eggs, crab legs, energy drinks, Legos, sneakers, pharmaceuticals, pistachios – if you can ship it, it’s being stolen, with organized criminals now wielding cyber-tradecraft to pilfer freight.
A Digital Hijack, Not a High-Speed Chase
The numbers are stark. Verisk CargoNet flagged around $725 million in cargo crime losses across North America in 2025. The FBI’s IC3 reported a staggering $21 billion in cybercrime losses for the same period. These figures, immense as they are, only scratch the surface, as both cargo theft and cyberattacks often fly under the radar, particularly for smaller private companies. Yet, these two seemingly disparate worlds are increasingly converging.
The cargo losses plaguing the transportation sector aren’t the product of masked figures with crowbars. No, these are the silent, insidious results of a successful phishing email, leading to a fraudulent pickup of a high-value pharmaceutical load destined not for a pharmacy, but a criminal warehouse. Industry estimates suggest that a significant portion of cargo crime in the United States now carries a cyber-enabled component, forcing a radical paradigm shift for a security community accustomed to viewing cargo crime as a purely physical threat. These aren’t petty thieves; many are international organized crime groups, operating with tactics chillingly familiar to anyone involved in traditional cyber incident response.
Their techniques are immediately recognizable to anyone who has been involved in incident response related to traditional cybercrime.
The Familiar Kill Chain, Applied to Cargo
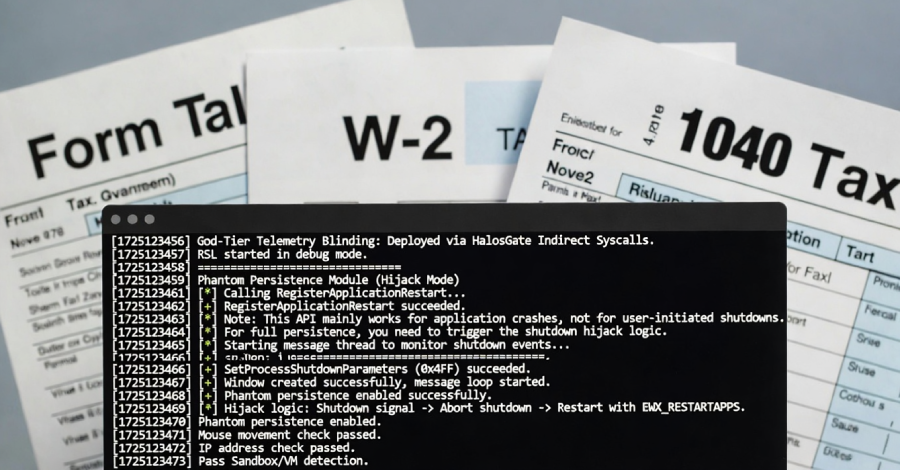
It begins innocuously, just like so many digital heists. Reconnaissance. Threat actors scour public data – USDOT numbers, FMCSA registry details, motor carrier numbers, insurance information, even employee data. Then, the phishing emails land, targeting staff in dispatch, customer service, or accounting – anyone with access to sensitive shipment information. Credentials are stolen, email accounts compromised. So far, textbook cybercrime.
This is where the paths diverge, where the attack spills out of the digital realm and into the operational space. Instead of pivoting into a corporate network to deploy ransomware, the attacker use the compromised email account to eavesdrop on communications. They’re listening for shipment notifications, new load tenders, bills of lading for active shipments. From this vantage point of trust, they subtly inject themselves into the conversation. A minor tweak to a pallet count here, a destination change there, a falsified piece of information designed to reroute a legitimate freight load to a controlled delivery point.
Alternatively, they might spin up a new, fraudulent carrier with the FMCSA, using stolen but legitimate identification details from an actual fleet. These imposter carriers then book real loads from legitimate load boards. The catch? The professional truck drivers picking up these loads often have no clue they’re unwittingly participating in a large-scale crime. They simply believe they’re working for a legitimate company.
Once the cargo reaches the criminal warehouse, it’s often broken down, cross-docked, or re-shipped under yet more falsified paperwork, effectively laundering it back into the supply chain. Many of these stolen consumables, especially those with limited shelf life, are sold and consumed within days, turning the recovery of stolen freight into an arduous, often futile, endeavor. By the time the legitimate shipper, broker, or carrier realizes what’s happened, the freight is long gone, the fraudulent carrier has vanished, and they’re left facing potentially catastrophic financial liabilities. A single trailer of pharmaceuticals? Millions. A load of pistachios? Hundreds of thousands. These aren’t minor inconveniences; these are devastating losses that the average small to mid-sized fleet simply can’t absorb. The digital revolution has arrived in cargo theft, and it’s here to stay.
Why Does This Matter for Developers?
Look, it’s easy to dismiss this as a logistics problem, a physical security issue. But here’s the thing: the initial breach, the entry point, is overwhelmingly digital. Developers are building the systems that logistics companies rely on – the transport management systems, the customer portals, the communication platforms. Understanding how these tools can be weaponized, how a seemingly innocuous credential compromise can lead to millions in stolen goods, is paramount. It’s not just about preventing data breaches anymore; it’s about securing the entire physical manifestation of digital information. This means strong authentication, strict access controls, and designing systems with an adversarial mindset – knowing that the next attack might not be aimed at your database, but at the very trucks leaving your loading dock.
Will This Replace Traditional Cargo Theft?
This isn’t a replacement so much as a powerful augmentation. Traditional, physical hijackings still occur, but they’re often more visible and risky. Cyber-enabled cargo theft is stealthier, more scalable, and exploits vulnerabilities in the digital infrastructure that underpins modern logistics. Think of it as upgrading from a brute-force lockpick to a sophisticated exploit that bypasses the lock entirely. The digital vectors allow for a level of planning and execution that physical methods struggle to match, making it the preferred method for sophisticated, organized criminal enterprises.
🧬 Related Insights
- Read more: ChipSoft Ransomware Cripples Dutch Hospitals’ EHR Backbone
- Read more: Grafana’s AI Feature Was One Sneaky Web Page Away from Spilling Secrets
Frequently Asked Questions
What is cyber-enabled cargo crime? Cyber-enabled cargo crime refers to cargo theft where cybercrime tactics, such as phishing, credential theft, and email compromise, are used to facilitate the physical theft of goods during transportation.
How much cargo is stolen using cyber tactics? Industry estimates suggest that a majority of cargo crime in the United States now involves a cyber-enabled component. Millions of dollars in goods are lost annually due to these methods.
Is my company at risk if we don’t use digital systems? While the initial breach is digital, the impact is physical. If your company interacts with the logistics ecosystem – receiving orders, coordinating shipments, managing invoices – you are indirectly exposed to the vulnerabilities exploited by these cybercriminals.