The handcuffs clicked shut, not on a shadowy cybercriminal cartel leader, but on a 15-year-old. This isn’t a morality play about prodigies gone rogue; it’s a stark market failure. France Titres, the nation’s issuing authority for everything from driver’s licenses to identity cards, found its digital doors kicked in, its data harvested. And who’s allegedly selling the spoils? A minor, using the handle ‘breach3d,’ on a cybercriminal forum.
The Paris Prosecutor’s Office confirmed the breach, the authenticity of the data offered for sale, and the subsequent detention. The timeline is tight: April 13th, ANTS (Agence Nationale des Titres Sécurisés) detected unusual network activity. By April 16th, authorities were alerted. The alleged perpetrator, operating under ‘breach3d,’ is accused of trying to offload between 12 and 18 million records. That’s not just a few thousand logins; it’s a significant chunk of the French populace’s administrative data.
What Exactly Was Stolen?
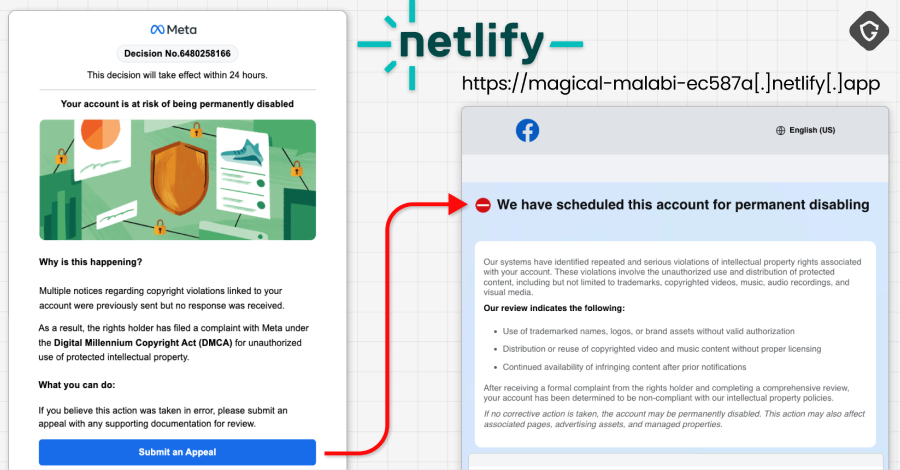
The agency eventually disclosed that the compromise impacted individual and professional accounts on the ants.gouv.fr portal. What wound up in the digital marketplace? Full names, email addresses, dates of birth, postal addresses, and phone numbers. The agency’s attempt to downplay the severity—stating the data “could not be used for unauthorized access”—rings hollow. Personal identifiers like these are the bedrock of identity theft and sophisticated phishing campaigns. It’s the raw material; the exploitation is merely a subsequent business model.
The juvenile faces serious charges: unauthorized access, persistence within systems, and data exfiltration from a state-run personal data processing system. He’s also accused of possessing the tools to commit these offenses. The potential sentence? Up to seven years in prison and a €300,000 fine. A judge is now weighing the evidence, with prosecutors pushing for formal charges and judicial supervision. This case underscores a grim reality: the barrier to entry for high-impact cybercrime is collapsing.
This incident isn’t merely about a French government agency; it’s a global signal. It mirrors the trend where increasingly sophisticated attacks are executed by individuals or small, agile groups, often with lower overheads than traditional criminal enterprises. The age of the alleged perpetrator is less a scandal and more a symptom of a digital ecosystem where vulnerabilities are commodities and the tools for exploitation are readily available, even to those with limited resources and perhaps even less mature moral compasses.
Is This a Sign of Things to Come?
The sheer scale of the ANTS breach, coupled with the alleged involvement of a minor, raises uncomfortable questions about the security posture of critical national infrastructure. When a 15-year-old can allegedly breach an entity responsible for issuing official documents, what does that say about the defenses in place? It suggests that the attack surface is vast and that defenders are often playing catch-up, reacting to threats rather than proactively neutralizing them. The market for stolen data is strong, and the allure of quick profit, particularly for those with fewer life constraints, is a potent motivator.
The government agency determined that among the affected data types were full names, email addresses, dates of birth, postal addresses, and phone numbers.
The agency’s subsequent announcement—that the number of impacted accounts was 11.7 million—is a slightly more precise figure than the threat actor’s claim of up to 19 million records. Yet, the core issue remains: millions of sensitive personal data points are now in circulation, or have been offered for sale, by a single, alleged perpetrator.
This isn’t just about a single breach; it’s about the systemic risk. The data exfiltrated from France Titres isn’t just a static list; it’s an asset that can be repackaged, cross-referenced with other stolen datasets, and used to build highly convincing social engineering attacks. The sophistication isn’t always in the exploit itself, but in how the stolen data is weaponized. A date of birth, a postal address, an email—these are the breadcrumbs that lead to deeper infiltration.
The market dynamics here are brutal. For the attacker, the cost of entry—a stolen credential or a successful exploit—is relatively low compared to the potential payout from selling the data on dark web marketplaces. For the victims—both the agency and the individuals whose data was compromised—the costs are immense and long-lasting, ranging from reputational damage to the potential for financial fraud and identity theft. This young perpetrator, if convicted, will face legal consequences, but the true cost is borne by millions.
The Data Breach Ecosystem
We’re seeing a bifurcation in the threat landscape. On one end, you have nation-state actors with sophisticated tools and objectives. On the other, you have opportunistic actors, sometimes driven by profit, sometimes by malice, and sometimes—as this incident suggests—by a blend of youthful audacity and access to a readily available black market. The France Titres breach highlights the vulnerability of government agencies, often perceived as having strong security, yet clearly not impenetrable. The continued existence of these data brokerages on the dark web fuels the cycle of breaches. Until the demand for stolen data is significantly curtailed, the supply will continue to flow, often facilitated by individuals operating with minimal oversight.
The potential for this information to be used in follow-on attacks is substantial. Imagine a phishing email that perfectly mimics communications from another French government agency, complete with your name, address, and date of birth. It’s not science fiction; it’s the direct consequence of data breaches like this. The notion that the stolen data can’t be used for unauthorized access feels like a lawyer’s footnote rather than a security guarantee. This data, in the wrong hands, is a powerful weapon.
🧬 Related Insights
- Read more: Metasploit’s March 2026 Update Arms Attackers Against Printers, Dev Spaces, and Email Gateways
- Read more: Rapid7 Keynote: Special Forces Mindset for Cyber Ops?
Frequently Asked Questions
What does France Titres (ANTS) do? France Titres is the French government agency responsible for issuing and managing administrative documents like driver’s licenses, identity cards, and vehicle registration certificates.
What kind of data was stolen in the ANTS breach? The stolen data includes full names, email addresses, dates of birth, postal addresses, and phone numbers from individual and professional accounts on the ants.gouv.fr portal.
Could this breach lead to identity theft? Yes, personal information like names, addresses, and dates of birth are commonly used in identity theft and sophisticated phishing attacks. While the agency stated it couldn’t be used for unauthorized access, its circulation poses significant risks.