
QR Codes Turn Traffic Texts into Data Heists
Your phone buzzes. A text from 'court services' screams unpaid traffic fine. Scan the QR? Kiss your bank details goodbye.

Your phone buzzes. A text from 'court services' screams unpaid traffic fine. Scan the QR? Kiss your bank details goodbye.

Ever wonder if that GenAI tool your company rushed out is a ticking bomb? OWASP's latest update on 21 risks and a tools matrix says yes—and demands you listen up.

You're scrolling LinkedIn, desperate for work in this brutal market, and bam—a Ferrari recruiter wants to chat. Don't click. It's stealing your passwords, MFA and all.

What if the next update to your favorite npm package came laced with North Korean spyware? That's exactly what happened to Axios — and it started with a too-perfect Slack invite.

Half of enterprises are cruising on ancient mobile OS versions. Jamf's massive device scan paints a brutal picture of the expanding mobile attack surface.

North Korean hackers didn't just steal $285 million from Drift—they did it in 10 seconds flat. DeFi's house of cards just collapsed again.

Drift got nonce'd. Hard. North Korea's hackers just turned social engineering into high art, draining $285 million from a 'secure' Solana DEX.

Iran just named names: Apple, Microsoft, Google, and more on a hit list with an April 1 deadline. Tech's globalization dream hits a brutal reality check.
Our honeypots caught dozens of probes yesterday alone, all wielding CVE-2025-30208 against Vite's @fs shortcut. Devs: your quick-setup tool just became a backdoor.

Imagine deploying an AI agent to streamline your ops—only for it to morph into a spy rifling through your cloud secrets. Vertex AI's default setup makes this nightmare real.
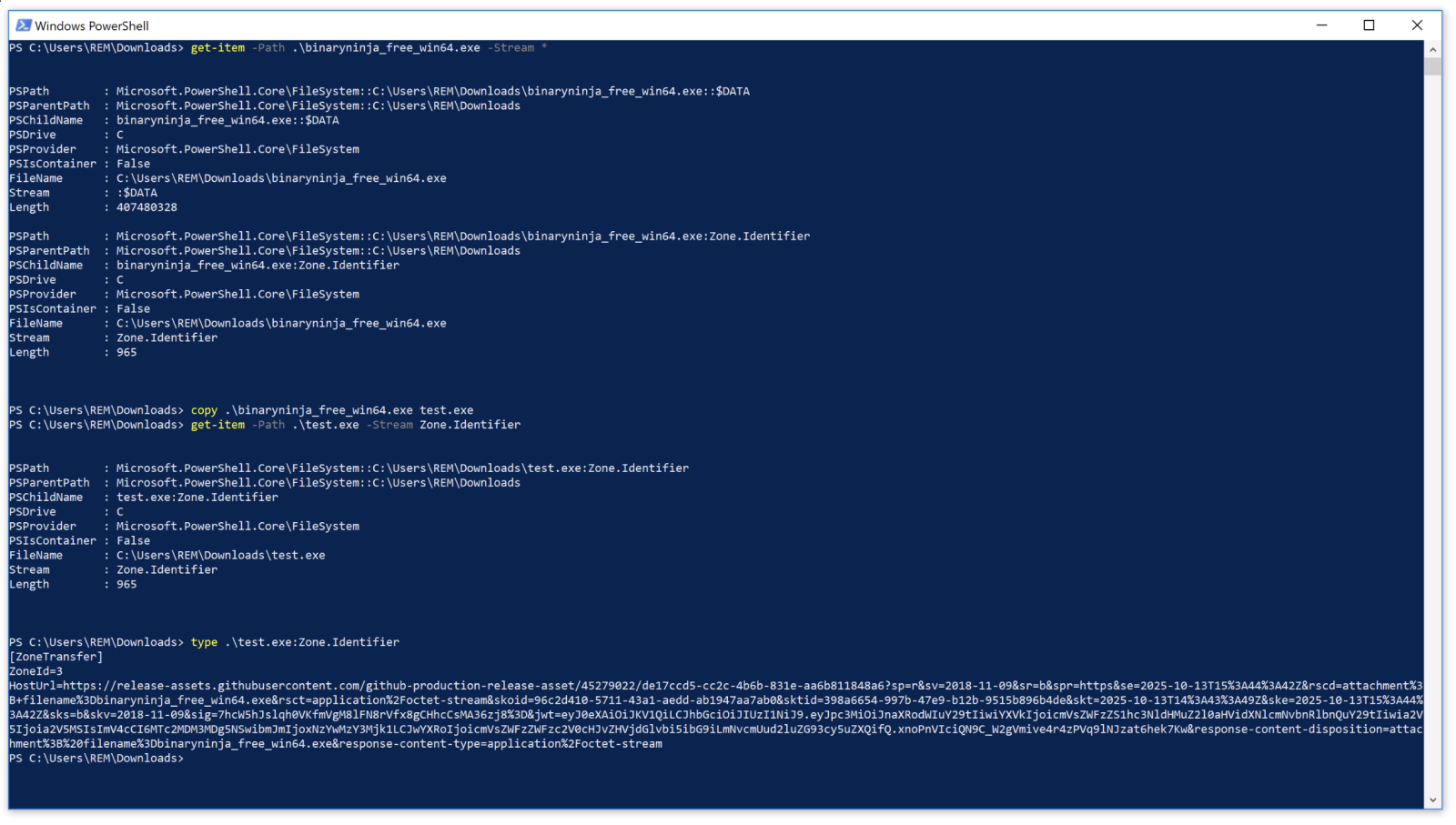
Imagine malware that doesn't just hide its tracks; it pours bleach on them. This script erases Windows' Zone.Identifier ADS post-copy, fooling forensics into thinking it's local-born.

Imagine your video call app turning into a hacker's playground. That's TrueConf's nightmare: a zero-day flaw letting attackers poison updates across government networks.
Anthropic's Claude Code hit a double whammy: a source leak followed by a permission system flaw that skips deny rules entirely. Developers, your SSH keys might be next if you're not careful.

Your firewall's breached. Do you call the feds—or hack back? The 2026 US Cyber Strategy just cracked the door to corporate cyber revenge.

DeepLoad isn't your grandpa's virus—it's AI-boosted, credential-grabbing malware slipping past defenses via social engineering and code bloat. Enterprises, wake up: this one's persistent and evolving.

Three bugs. Two hours. Pixel 9's BigWave driver hands attackers the keys to kernel town. Google's sandbox? Laughable.

Imagine malware that doesn't pack up and leave after grabbing your passwords. Venom Stealer sticks around, slurping data continuously—turning your machine into a perpetual leak.

Four billion malicious sessions. 78% slip through IP reputation nets via sneaky residential proxies. Defenses built on bad assumptions are crumbling.

Your next browser login could hand hackers remote control—without them ever cracking it on your PC. Storm infostealer just upped the ante on credential theft.

Ransomware just hit warp speed. Akira's crew wraps up the whole heist—access, exfil, encrypt—in less than 60 minutes, leaving victims scrambling.