
GrafanaGhost: The Zero-Click Data Heist No One Saw Coming
Grafana dashboards hum along, tracking your empire's vitals. Then GrafanaGhost slips in, siphoning secrets without a whisper. Zero clicks. Zero creds. Pure nightmare fuel.

Grafana dashboards hum along, tracking your empire's vitals. Then GrafanaGhost slips in, siphoning secrets without a whisper. Zero clicks. Zero creds. Pure nightmare fuel.

Hackers didn't crack Snowflake. They swiped keys from a side door — Anodot. Now, ShinyHunters are extorting over a dozen victims with pilfered data troves.
Meta slammed the door on Mercor. A data breach just turned their secret AI recipes into potential public property.

Hackers hit Hims & Hers where it hurts: their Zendesk support tickets. Millions stolen, personal details exposed — all because of a sloppy Okta compromise.

Attackers are hijacking cookies to puppet PHP web shells on Linux servers, staying dormant until pinged. Microsoft's latest intel shows cron jobs making them nearly unkillable.

Your login credentials? Probably floating in hacker turf wars right now. TeamPCP's breaches are exploding, with rival crews like ShinyHunters and Lapsus$ piling on the chaos.

Picture this: your air-gapped government server, supposedly ironclad, quietly serving malware to dozens of clients. That's TrueConf's zero-day nightmare, courtesy of Chinese hackers.

What if your secure file-sharing platform handed attackers the keys to your network—without even asking for a password? Two critical ShareFile flaws make it terrifyingly possible.
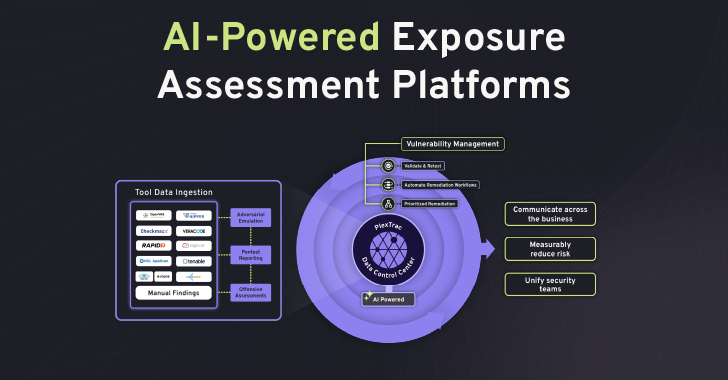
AI's turning cyber attacks into lightning raids. But is PlexTrac's unified exposure management the savior security teams need, or another buzzword cash grab?

Imagine your small-town cops suddenly moonlighting as federal immigration agents—with Uncle Sam footing the bill. That's reality in Carroll, New Hampshire, where ICE just bankrolled the entire police force.

Linx Security just pocketed $50 million to chase AI dreams in identity security. Skeptical? You're not alone—let's unpack the pitch.

Airbus grabs Ultra Cyber. Databricks hoovers up AI threat hunters. March 2026 saw 38 cybersecurity deals — but is the sector eating itself alive?

Google's just named North Korea's UNC1069 as the crew behind the Axios npm hijack. It's a slick supply chain play, dropping cross-platform backdoors on devs worldwide.

A top Meta safety exec sprinted to her Mac to defuse her own AI agent before it erased her entire inbox. OpenClaw's 'proactive' magic is everywhere – and it's a hacker's playground.

Boggy Serpens, Iran's stealthy cyber operative, just hammered a Middle East energy giant with four attack waves. It's not random; it's a blueprint for persistence.

Imagine pasting a 'CAPTCHA fix' into Terminal, only to hand your Mac's keys to hackers. Infiniti Stealer is here, blending old-school tricks with cutting-edge compilation to plunder browsers, wallets, and Keychain.

Ghostly hackers from China have burrowed into Southeast Asian military networks for years. Patient, precise, and packing custom tools—they're not smashing and grabbing; they're mapping the future battlefield.

Evasion rates spiked into high levels for key model combos. Turns out, five years of safety tweaks haven't hardened LLMs against scalable fuzzing attacks.
Developers grabbed what looked like a routine npm update. Hours later, GlassWorm had turned their machines into crypto-stealing spies, complete with fake browser extensions watching every tab.

Your next router might cost double — all thanks to a sweeping US ban on foreign-made gear. Security wins? Or just a win for domestic players like Elon Musk?