
Juniper's Junos OS Nightmare: 36 Flaws That Could Hand Attackers Your Network Keys
Your company's routers just got a wake-up call. Juniper's patching 36 holes in Junos OS that scream 'hack me,' from default passwords to root escalations.

Your company's routers just got a wake-up call. Juniper's patching 36 holes in Junos OS that scream 'hack me,' from default passwords to root escalations.

Forget the usual regional squabbles. A hack-for-hire crew tied to India's Bitter APT just went after MENA journalists with slick phishing that nearly cracked Apple and Google accounts. This isn't local drama—it's a sign of Delhi's digital tentacles stretching far.

Forget the headlines about nation-state hacks on big corps. Russia's APT28 is after your living room router, turning SOHO gear into a global spy network. Time to check your DNS settings—now.

Bitcoin Depot's IT systems cracked open on March 23, letting thieves siphon 50 Bitcoin worth $3.6 million. It's not their first rodeo, and crypto ATM operators are sweating the fallout.

CISA dropped a bombshell advisory on April 7: Iranian hackers are already inside US water plants and energy grids, fiddling with PLCs that control the pumps and valves. It's not theory—it's happening now, and the fixes sound painfully basic.
Picture this: your shiny new AI agent, deployed with a few CLI commands, suddenly reads every other agent's secrets. AWS Bedrock AgentCore's starter toolkit just made privilege escalation child's play.

Attackers slipped malicious PDFs past Adobe Acrobat Reader's defenses starting December. Months of silent exploitation demand immediate patching.

65% of 2023 breaches crossed OS boundaries—Windows to MacBooks, Linux servers in between. SOCs scramble; here's how the sharp ones don't.

Forget the flashy breaches. The real killer is the endless grind of password resets and lockouts draining your IT team dry. It's not just annoying—it's expensive.
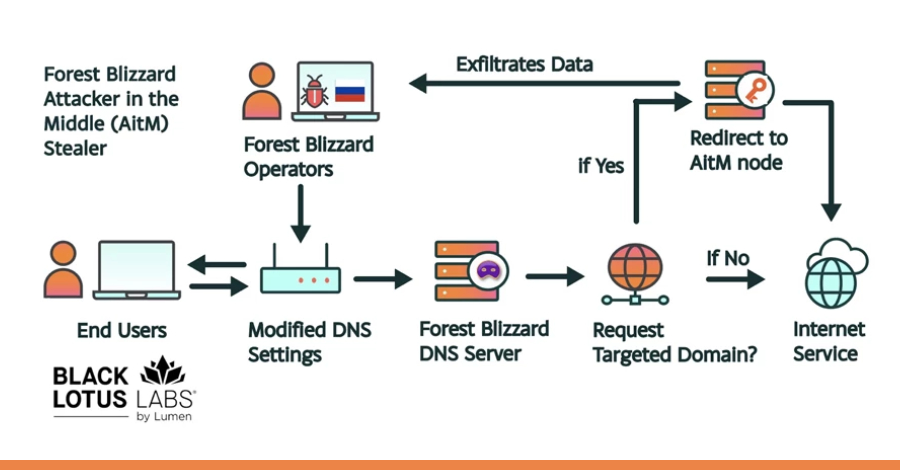
Imagine your dusty home router silently funneling your login credentials to Moscow. That's APT28's FrostArmada in action—18,000 devices compromised across 120 countries.

Forget the headlines — this hits real German businesses that shelled out €1.9M or watched servers die. BKA's got names, but ransomware's hydra heads just grow back.

Your local hospital's servers go dark. Patients wait in limbo. That's the grim reality of Storm-1175's zero-day ransomware rampage — and it's just getting started.

Your online banking app? It might harbor a 20-year-old vulnerability Claude Mythos just found. Great for defenders — terrifying if attackers grab it first.

Your next spreadsheet might be AI-spun and gone in hours—secure or sitting duck? Instant software flips cybersecurity on its head, arming attackers and defenders alike.

One pip install, and your AWS keys were gone. The LiteLLM attack shows developer laptops aren't just tools—they're attacker playgrounds loaded with plaintext secrets.

Spotlights blazing on the RSAC 2026 stage, demos of AI agents dismantling simulated ransomware in seconds. But beneath the wow factor, cracks in the architecture hint at tomorrow's nightmares.

Forget the old-school supply chain hits that took months to plan. PRT-scan shows AI automating GitHub attacks, scanning thousands of repos for dumb misconfigs in hours.

Fortinet's endpoint management server is bleeding from two zero-day wounds. Attackers are already feasting – time to patch or perish.

We all figured Axios was untouchable, that rock-solid HTTP client millions rely on. But hackers didn't crack code—they conned humans, at industrial scale.
Everyone figured it'd be a quiet week post-patches. Instead, scams hijacked dream jobs, AI sparked bot wars, and supply chains took fresh hits—shifting how we guard credentials and code.