The public internet. A cesspool. And on April 19th, 2026, a familiar stench wafted through a honeypot sensor: the Outlaw botnet, alias mdrfckr, was back, and it had upgraded its toolkit.
Look, we’ve all been here before. The same old malware, the same old playbook. The SHA-256 hash a8460f446be540410004b1a8db4083773fa46f7fe76fa84219c93daa1669f8f2 is practically a museum exhibit by now. VirusTotal flagged it way back in 2018. It’s the signature of the mdrfckr campaign, a seven-year-old persistent threat known for its authorized_keys file hijacking, chattr -ia .ssh defensive maneuvers, and chpasswd account takeovers.
This isn’t a grand new campaign announcement. The core attack vectors? Old news. The persistence mechanism? Ancient history. What this observation adds is a subtle, yet critical, update: the botnet is now sporting a third major version of its libssh client. And if you’re still relying on signatures from yesteryear, you’re going to miss it.
Is This Just Another Update, or Something More?
For nearly seven years, the mdrfckr campaign has been a stubborn thorn in the side of network defenders. Trend Micro first pinned it to the Outlaw/Dota family in 2018. Since then, Anomali, Yoroi, Juniper, and a host of others have documented its methods. The recon sequences, the competitor cleanup scripts – all well-trodden ground. The signatures used for detection? Apparently, they’re still stuck in the past.
In late 2022 and early 2023, the port22.dk blog provided a deep dive. They identified a primary SSH client banner, SSH-2.0-libssh-0.6.0/SSH-2.0-libssh-0.6.3, tied to a hassh fingerprint 51cba57125523ce4b9db67714a90bf6e. Ninety-nine percent of observed attacks used this. Then, a pivot. By December 2022, the campaign shifted to SSH-2.0-libssh_0.9.5/SSH-2.0-libssh_0.9.6, represented by hassh f555226df1963d1d3c09daf865abdc9a. This second iteration accounted for a massive number of attacks. They also added new command variants – chattr -ia .ssh; lockr -ia .ssh, and even just lockr -ia .ssh on its own. This wasn’t just minor tinkering; it was adaptation.
Jesse La Grew at SANS ISC noted these split commands in May 2023. Guy Bruneau at DShield echoed this, explicitly linking the playbook to Outlaw. This is the public timeline, and my sensor just added a new chapter.
The April 2026 Glitch
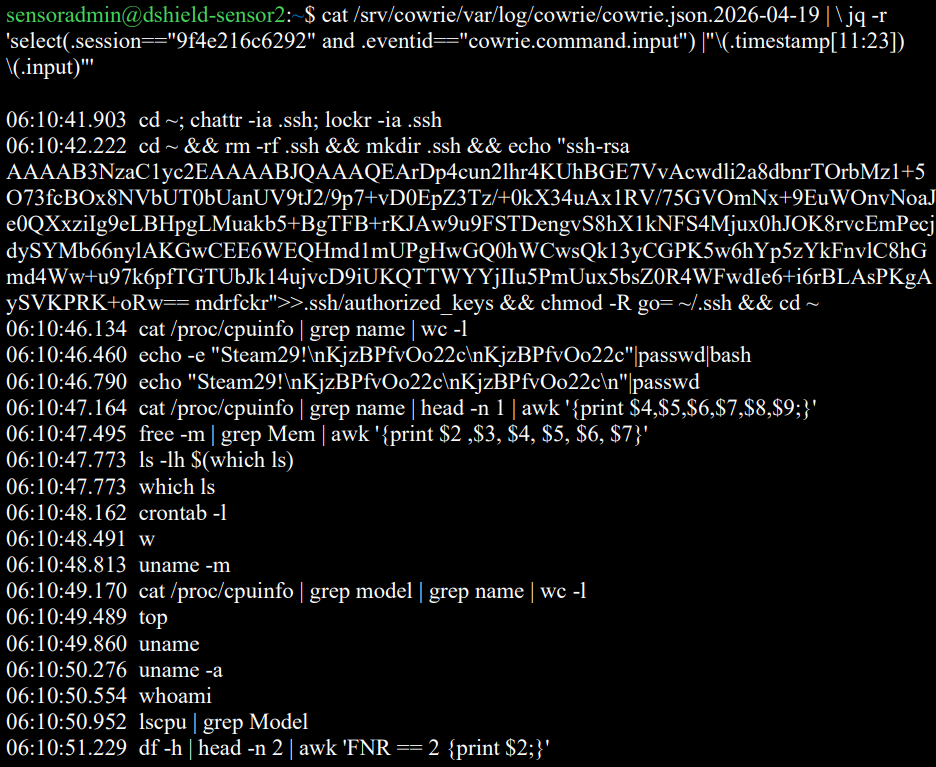
Between April 14th and April 21st of 2026, my DShield sensor caught a familiar tune: the mdrfckr campaign. Twenty-four unique IP addresses hammered the sensor, writing that same old SHA-256 hash (a8460f446be540410004b1a8db4083773fa46f7fe76fa84219c93daa1669f8f2) into /root/.ssh/authorized_keys and other compromised locations. A total of 229 authorized_keys modifications across 1,230 SSH sessions. Over 4,000 post-authentication commands executed.
The action peaked on April 19th. Twenty of those IPs connected within a mere 131-second window. The remaining four showed up on neighboring days, but they ran the exact same playbook with the exact same key.
And the commands? Identical to the post-December-2022 split variant: chattr -ia .ssh followed by the key write.
The real news? The SSH client.
The New Hassh: libssh 0.11.x - A Ghost in the Machine?
Every single one of those 24 IPs was broadcasting SSH-2.0-libssh_0.11.1. This generated a hassh fingerprint of 03a80b21afa810682a776a7d42e5e6fb. This fingerprint, crucially, doesn’t match any of the hashes documented in previous reports.
| Reporting period | Hassh fingerprint | Client banner | Source |
|---|---|---|---|
| Oct–Nov 2022 | 51cba57125523ce4b9db67714a90bf6e |
SSH-2.0-libssh-0.6.0 / SSH-2.0-libssh-0.6.3 |
port22.dk |
| Dec 2022+ | f555226df1963d1d3c09daf865abdc9a |
SSH-2.0-libssh_0.9.5 / SSH-2.0-libssh_0.9.6 |
port22.dk |
| May 2023 | f555226df1963d1d3c09daf865abdc9a |
SSH-2.0-libssh_0.9.5 / SSH-2.0-libssh_0.9.6 |
SANS ISC, DShield |
| Apr 2026 | 03a80b21afa810682a776a7d42e5e6fb |
SSH-2.0-libssh_0.11.1 |
DShield Sensor |
This is the whole point. The mdrfckr campaign, a known persistent threat, has evolved. It’s not just regurgitating old code. It’s updating its tools. If your threat detection is hardcoded to look for libssh-0.6.x or libssh-0.9.x fingerprints, you’re looking at a ghost.
Detection Engineering: Stop Chasing Shadows
So, what’s the takeaway here? Don’t get complacent. The malware authors aren’t. They’re out there, tinkering, updating, and adapting. If you’re a handler maintaining rules for Outlaw/mdrfckr, you need to update your signatures.
Attributing this to Outlaw isn’t the novel part; it’s the methodology of continuous tracking and adaptation. The historical context is crucial. This isn’t a new threat actor; it’s an old one with new tricks. The campaign’s longevity itself is a proof to its adaptability, but its continued reliance on a consistent core infrastructure—the same a8460f446be540410004b1a8db4083773fa46f7fe76fa84219c93daa1669f8f2 hash for authorized_keys—while updating the client library indicates a focused, if not particularly sophisticated, approach to evading detection. It’s the digital equivalent of changing your coat but keeping your face.
This isn’t about a “game-changing” breakthrough; it’s about the tedious, unglamorous work of keeping up. The persistence comment string mdrfckr has been around longer than some junior analysts. If your rules are pinned to specific, older hassh values for the libssh client, they’re effectively useless against this latest iteration. It’s like showing up to a cybersecurity conference with a floppy disk – quaint, but utterly ineffective.
The core insight here is that the campaign’s infrastructure (the authorized_keys file, the persistence mechanism) remains stable, while the client library is a moving target. This offers a distinct opportunity: while specific libssh versions might change, the overall fingerprinting of SSH clients, especially with known vulnerable versions or common configurations, can still be a valuable detection vector. It’s a reminder that threat intelligence isn’t a static report; it’s a living, breathing thing that requires constant feeding and updating.
🧬 Related Insights
- Read more: VMware Fusion Patch: High-Severity Flaw Exposed
- Read more: [5 Mythos Myths Busted] Anthropic’s Security Hype
Frequently Asked Questions
What does the mdrfckr campaign do?
The mdrfckr campaign is a persistent botnet that compromises systems, installs itself via SSH, and often cleans up competitor malware. It primarily uses authorized_keys manipulation for persistence.
Will this new libssh version make Outlaw malware undetectable?
No, but older detection rules based on previous libssh versions will miss it. Updated signatures and behavioral analysis are necessary for detection.
Is this a new malware family?
No, this is an update to an existing, well-documented campaign (Outlaw/mdrfckr) that has been active for years. The core malware and tactics remain similar, with an updated client library.