The glow of a monitor casts long shadows in a darkened room, the cursor blinking rhythmically, a tiny sentinel against the vast, digital unknown.
And what a week it’s been in that unknown! We’re witnessing not just advancements, but a fundamental platform shift, an AI-fueled acceleration across the cyber landscape. It’s like the invention of the printing press combined with the discovery of electricity, all happening at hyperspeed.
The Good: Cracking the Code on Digital Criminals
First off, a round of applause for the authorities. They actually snagged Xu Zewei, an alleged Chinese Ministry of State Security (MSS) contract hacker, and he’s now headed to the U.S. to face the music. This isn’t just one guy; he’s supposedly tied to the Silk Typhoon group, a bunch that spent at least a year, from February 2020 to June 2021, on a highly coordinated intel-gathering spree. Their targets? Critical COVID-19 research outfits. They were after vaccine and treatment data, and they got it by exploiting zero-day vulnerabilities in Microsoft Exchange Servers, planting web shells deep within networks. The Department of Justice wants him for multiple counts of computer intrusions and conspiracy. This feels like finally catching a phantom, a significant win in the ongoing digital arms race.
Then there’s the takedown of a massive crypto investment fraud network across Europe. Over €50 million vanished, gone, poof! These guys were running a slick operation, almost like a legitimate business, with up to 450 people spread across call centers in Albania. They’d reel people in with online ads, then “retention agents” would wear down victims with relentless pressure and remote access to manipulate their deposits. The money flowed through international laundering pipelines, but justice, it seems, has a way of catching up.
And speaking of money, Evan Tangeman is looking at nearly six years for laundering a staggering $230 million from a crypto heist that ran from late 2023 to mid-2025. How’d they do it? They impersonated Gemini customer support, hooked folks with remote desktop software, and bypassed two-factor authentication to nab thousands of Bitcoin. Tangeman’s job was to make that stolen cash disappear through mixers, exchanges, and VPNs. All to fund a criminal empire’s lavish lifestyle. It’s a stark reminder that even with the anonymity crypto seems to offer, skilled investigators and a bit of digital breadcrumbing can lead right to your door.
The Bad: Social Media’s Scammer Scourge
The FTC dropped a doozy of a report: social media fraud cost users a cool $2.1 billion in 2025. That’s an eightfold jump since 2020! Platforms like Facebook, Instagram, and WhatsApp are now the primary battlegrounds, snagging nearly 30% of all fraud victims. What’s wild is that Facebook alone spawned more losses than traditional text and email scams combined. This isn’t some fringe issue; it’s hitting every age group, a digital plague spreading through our feeds.
Malicious actors actively use platforms like Facebook, Instagram, and WhatsApp to exploit nearly 30% of all fraud victims last year.
These actors are sophisticated. They hijack accounts, study posts for the perfect social engineering bait, and even buy ads just like legitimate businesses. They’re not just casting a wide net; they’re filtering by age, interests, and shopping habits. It’s personalized deception on a massive scale. Meta’s fighting back, pulling down millions of scam ads and accounts last year, and rolling out new protections. Still, the warning remains: limit profile visibility, verify vendors independently, and be incredibly wary of investment advice from strangers online.
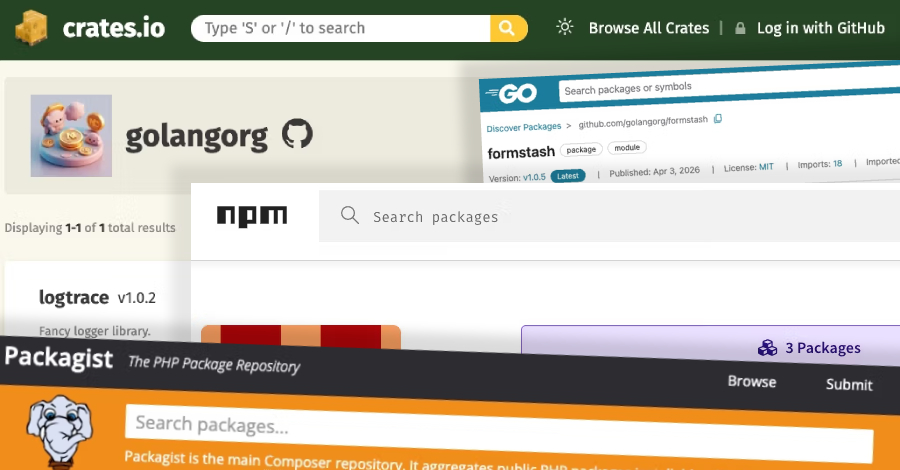
The Ugly: Code Chaos in the Supply Chain
But here’s where things get truly chilling for anyone who writes code or relies on software. Cybersecurity researchers are tracking a highly sophisticated supply chain attack targeting SAP-related npm packages. They’re calling it “Mini Shai-Hulud,” and it’s weaponized credential-stealing malware. The attackers zeroed in on vital packages within SAP’s cloud application development ecosystem, like @cap-js/[email protected] and others. The exploit? A gap in npm’s OIDC trusted publishing configuration, which allowed them to swap a token and sneak in poisoned packages. This is the digital equivalent of a builder unknowingly using tainted bricks in the foundation of a skyscraper. When this kind of malware gets into the supply chain, it can spread like wildfire, compromising countless systems and sensitive data before anyone even knows it’s there. It’s a terrifyingly efficient way to weaponize trust, a direct assault on the very infrastructure developers rely on.
This isn’t just about isolated incidents anymore; it’s about the interconnectedness of our digital world. Each week brings new marvels and new nightmares, a constant churn of innovation and exploitation. The AI revolution isn’t just coming; it’s here, and it’s reshaping the battlefield in ways we’re only just beginning to comprehend.
🧬 Related Insights
- Read more: CVE-2026-20929: Hackers Hijack Your Certs with DNS CNAME Tricks
- Read more: China APT ‘GopherWhisper’ Abuses Cloud Services [New Tactic]
Frequently Asked Questions
What is the main takeaway from the FTC’s social media fraud report?
The primary takeaway is that social media platforms are now the leading vector for fraud, with losses skyrocketing to $2.1 billion in 2025, surpassing traditional methods like text and email scams.
How did the “Mini Shai-Hulud” attack compromise SAP-related npm packages?
The attack exploited a configuration gap in npm’s OIDC trusted publishing, allowing threat actors to substitute a token and publish malicious versions of legitimate packages.
What does the extradition of Xu Zewei signify for cybersecurity?
It signifies a significant international law enforcement success in dismantling state-backed cyberespionage operations and holding individuals accountable for sophisticated network intrusions.