The Batch Script That Scrubs Windows ADS to Ghost Malware Persistence
Imagine malware that doesn't just hide its tracks; it pours bleach on them. This script erases Windows' Zone.Identifier ADS post-copy, fooling forensics into thinking it's local-born.
⚡ Key Takeaways
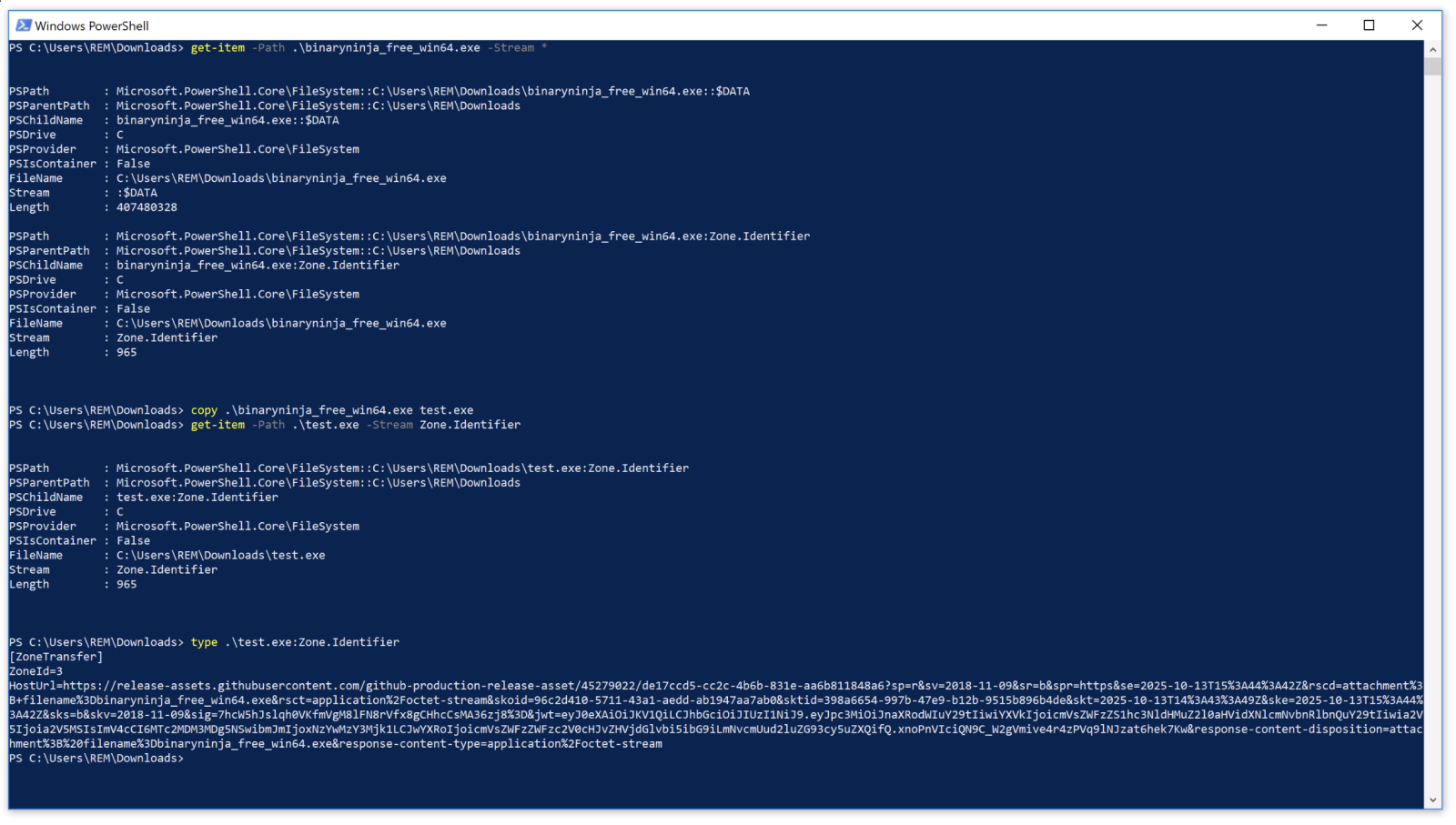
- Malware copies to APPDATA, then uses PowerShell to erase Zone.Identifier ADS, evading download-origin scans. 𝕏
- Persistence via obfuscated Run key value executes dwm.cmd at boot, mimicking legit processes. 𝕏
- LLMs incorrectly claim copies drop ADS; tests prove they preserve it, making removal a key evasion step. 𝕏
Worth sharing?
Get the best Cybersecurity stories of the week in your inbox — no noise, no spam.
Originally reported by SANS Internet Storm Center



