APT28's Router Trap: How Russian Hackers Are Siphoning Your Secrets Through Everyday WiFi Gear
Imagine your trusty router, that unassuming box in the corner, quietly handing your login details to GRU spies. Russia's APT28 just turned SOHO devices into credential vacuums, and the UK's NCSC is sounding the alarm.

⚡ Key Takeaways
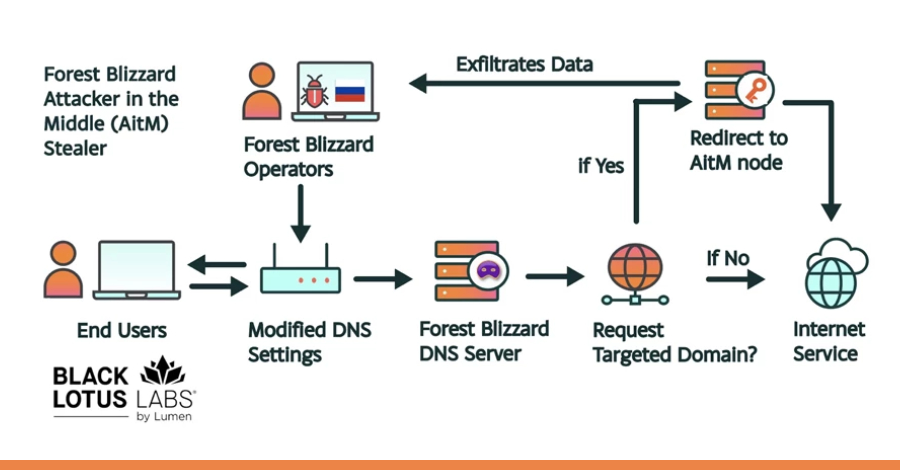
- APT28 exploits TP-Link and MikroTik routers via known CVEs to hijack DNS and steal credentials through AitM attacks. 𝕏
- NCSC attributes campaigns to Russia's GRU Unit 26165; opportunistic scanning leads to targeted intel grabs. 𝕏
- Mitigate with patches, MFA, and network segmentation—your SOHO router is prime prey. 𝕏
Worth sharing?
Get the best Cybersecurity stories of the week in your inbox — no noise, no spam.
Originally reported by InfoSecurity Magazine