The digital underworld hums with a new kind of danger. Imagine a master key, not just for one door, but for the entire building’s security system, and it’s being hawked for a song. That’s the chilling essence of PamDOORa, a newly disclosed Linux backdoor that’s sending ripples of unease through the cybersecurity community.
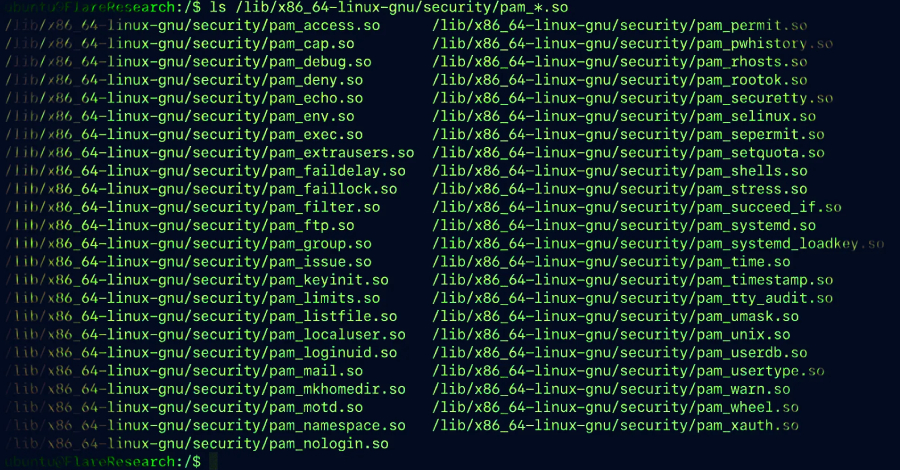
This isn’t just another piece of malware; it’s a sophisticated attack vector that plants itself deep within the Linux operating system’s authentication framework. Think of PAM (Pluggable Authentication Modules) as the incredibly flexible gatekeeper for your Linux server. It’s designed to be adaptable, allowing administrators to swap out authentication methods on the fly – from passwords to fingerprints, without rewriting applications. It’s a beautiful piece of engineering, meant to empower. But like any powerful tool, when it falls into the wrong hands, it becomes a formidable weapon.
And that’s precisely what’s happening here. PamDOORa, marketed by a threat actor known as “darkworm” on the Rehub Russian cybercrime forum, is essentially a backdoor that exploits this very flexibility. For a price—initially $1,600, now slashed to a frankly alarming $900—it offers persistent SSH access, the digital equivalent of a ghost in the machine, all initiated by a secret handshake: a magic password and a specific TCP port combination. It’s less about brute force and more about slipping through the cracks, a digital phantom.
The PAM Paradox: Power and Peril
This whole situation hinges on the inherent risk of PAM itself. Because these modules often run with the highest privileges—root access, in Linux terms—a single compromised or maliciously crafted module can be catastrophic. It’s like giving a spy access to the building’s master blueprint and the keys to every office. Group-IB has been sounding this alarm for a while, highlighting how even seemingly innocuous modules can be twisted. The pam_exec module, for instance, which is designed to run external commands, can be weaponized to inject malicious scripts, giving attackers a direct line to privileged shells and a path to stealthy, enduring presence.
PamDOORa seems to take this a step further. Flare.io, the researchers who detailed the backdoor, indicate it’s not just about getting in and stealing credentials—it’s about covering tracks. The malware reportedly boasts anti-forensic capabilities, meaning it actively tampers with authentication logs. It’s the digital equivalent of cleaning up fingerprints, erasing every trace of its presence. This makes detecting and investigating such breaches exponentially harder. It’s not just about breaking in; it’s about making sure you can’t even tell when they broke in.
“PamDOORa represents an evolution over existing open-source PAM backdoors,” Morag explained. “While the individual techniques (PAM hooks, credential capture, log tampering) are well-documented, the integration into a cohesive, modular implant with anti-debugging, network-aware triggers, and a builder pipeline places it closer to operator-grade tooling than the crude proof-of-concept scripts found in most public repositories.”
This quote is critical. It signals a shift from hobbyist hacking to professionalized cybercrime tooling. We’re moving beyond scattered scripts into something more polished, more deliberate. This isn’t just a proof of concept; it’s a product being refined and sold, designed for sustained, high-impact operations. The builder pipeline Morag mentions implies a degree of customization—allowing attackers to tailor the backdoor to specific targets, making each infection potentially unique and harder to generalize defenses against.
A New Era of Backdoor Sophistication?
While there’s no concrete evidence yet that PamDOORa is wreaking havoc in live attacks, the implications are staggering. The path to infection likely starts with an attacker gaining initial root access through other means—perhaps a vulnerability in a web application or a phishing scam. Once inside, they deploy this PAM module, and suddenly, every legitimate user authenticating through the system is a potential data source. Their SSH credentials, the keys to their digital kingdoms, are siphoned away. It’s like a parasite that feeds not just on the host’s energy, but on the very keys that allow the host to operate.
The fact that it’s being sold on a Russian cybercrime forum for a diminishing price is telling. It suggests either a lack of initial uptake from the high-end attackers, or a strategic move to make it more accessible. Either way, it lowers the barrier to entry for sophisticated espionage and data theft operations. This is the terrifying beauty of a platform shift in cybercrime—tools that once required deep expertise are becoming commoditized, accessible to a wider range of nefarious actors.
This is why understanding PamDOORa and its ilk matters. It’s a stark reminder that security isn’t a static fort to be built and then forgotten. It’s a dynamic battlefield. And the weapons are getting smarter, more insidious, and alarmingly accessible.